Cloud misconfigurations cause 82% of healthcare breaches. Learn which S3, IAM, and network settings put PHI at risk. Find them before attackers do.
Resources
Blog
Sprocket Security
Blogs by Sprocket Security

53% of connected medical devices have critical vulnerabilities. Learn how attackers and exploit IoT blind spots in healthcare networks and how to close them.
Daniel Barnes shares stories from his pentesting career and gives advice for up-and-coming offensive security professionals.
Learn what HHS OCR investigators look for after a HIPAA breach and how continuous penetration testing builds the audit trail that proves your security programs works.
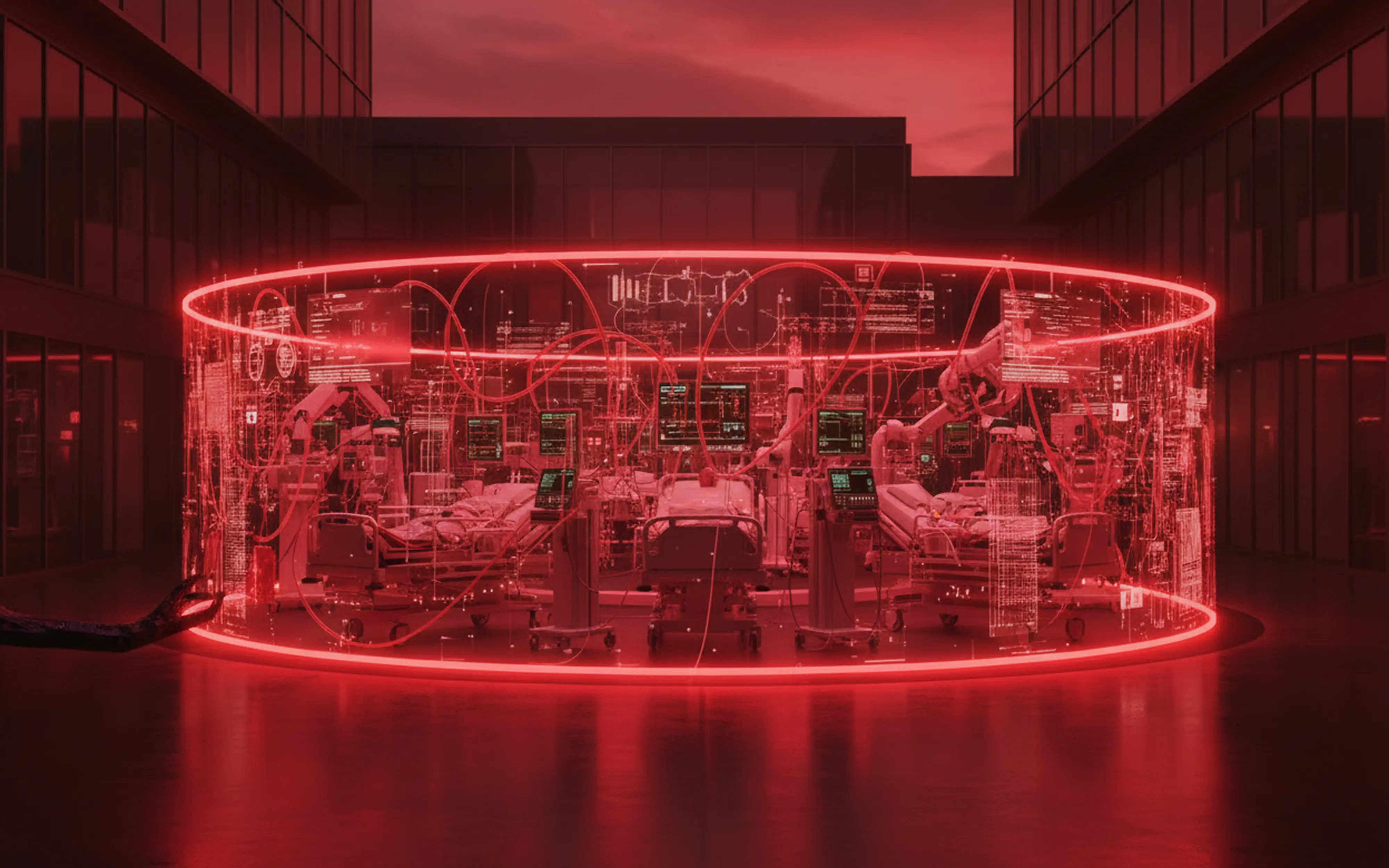
Healthcare ransomware exploits the gap between tests. See how continuous penetration testing reduces exposure, speeds remediation, and protects patient care.
Learn what DORA’s TLPT assessment requires, why most organizations fail on preparation (not vulnerabilities), and how to build a TLPT-ready security program.