The move to the cloud promised healthcare organizations agility, cost savings, and resilience. For the most part, it has delivered. But it has also introduced a category of security risk that is fundamentally different from anything that came before it — one where a single checkbox left unchecked, a single storage bucket set to the wrong permission level, or a single IAM role granted one too many privileges can expose millions of patient records to anyone on the internet.
Cloud misconfigurations are now the leading cause of healthcare data breaches. They are not the result of sophisticated nation-state attacks or zero-day exploits. They are the result of complexity — cloud environments that grow faster than the teams managing them, shared responsibility models that are misunderstood, and security controls that default to convenience rather than protection. Understanding what these misconfigurations look like, and where they hide, is the first step toward closing them.
The Scope of the Problem
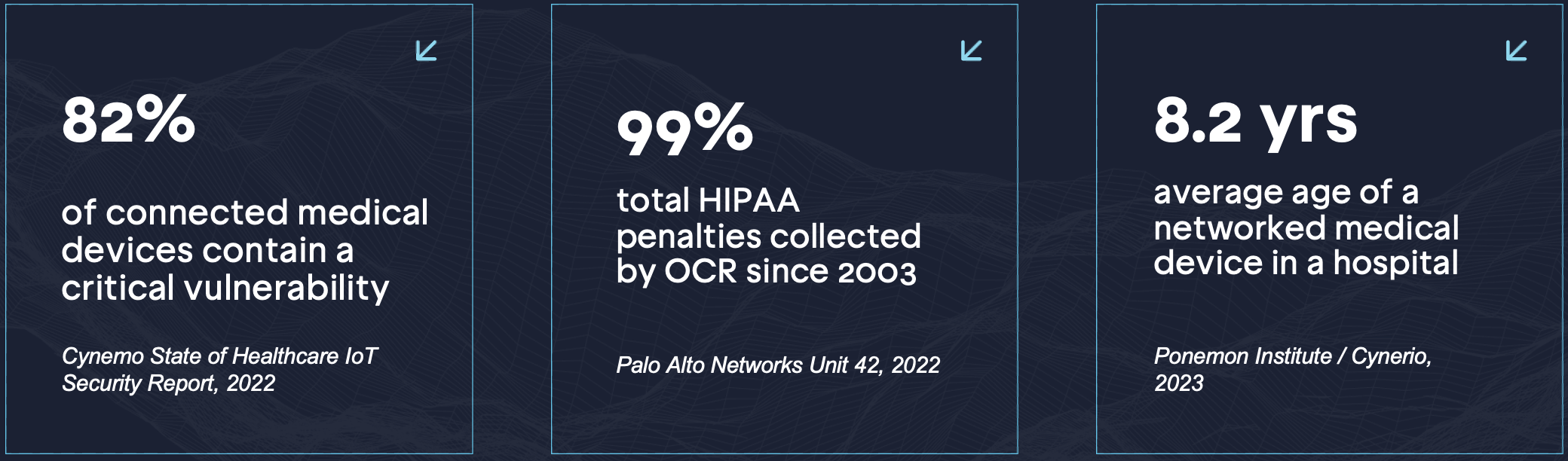
The numbers are difficult to ignore. According to IBM’s 2023 Cost of a Data Breach Report, 82% of healthcare data breaches now involve data stored in the cloud. Gartner has projected that through 2025, 99% of cloud security failures will be the customer’s fault — not the cloud provider’s — driven overwhelmingly by misconfiguration rather than platform vulnerabilities. And the financial consequences in healthcare specifically are severe: IBM and the Ponemon Institute put the average cost of a healthcare cloud security breach at $5.3 million, consistently higher than any other industry.
What makes cloud misconfiguration particularly dangerous in a healthcare context is the nature of what’s at stake. PHI is not just valuable to attackers for ransomware purposes — it commands a premium on dark web markets, where complete patient records sell for orders of magnitude more than credit card data. A misconfigured S3 bucket containing EHR exports or imaging data is not a theoretical risk. It is a target actively sought by automated scanning tools that index the public internet around the clock.
The Shared Responsibility Misunderstanding
The root of most cloud security failures in healthcare is a misunderstanding of the shared responsibility model. Cloud providers — AWS, Azure, GCP — are responsible for the security of the cloud: the physical infrastructure, the hypervisor, the underlying network. The customer is responsible for security in the cloud: access controls, encryption, network configuration, identity management, and data governance.
This distinction sounds straightforward. In practice, it is consistently misapplied. Healthcare IT teams accustomed to managing on-premises infrastructure assume that controls they previously handled at the hardware or network level are being handled by the cloud provider. They are not. The provider gives you the tools to configure those controls correctly. Whether you configure them correctly is entirely your responsibility — and, in the event of a breach, entirely your liability under HIPAA.
“The vast majority of cloud-based exposures we investigate are not the result of attackers finding new vulnerabilities. They are the result of organizations leaving doors open that they didn’t know existed.”
— Wiz Cloud Security Report, 2023
The Six Misconfigurations That Put PHI at Risk
Publicly exposed storage buckets remain the most common and most damaging misconfiguration in healthcare cloud environments. AWS S3, Azure Blob Storage, and Google Cloud Storage all require explicit configuration to restrict public access — and the default settings have historically been more permissive than most administrators realize. A single bucket containing patient discharge summaries, imaging results, or insurance claims, set to public access during a migration and never corrected, is a breach waiting to be discovered. Automated tools scan for exposed buckets continuously; the window between misconfiguration and discovery by a threat actor is measured in hours, not days.
Overpermissioned IAM roles are the second major vector. In cloud environments, the principle of least privilege is not enforced automatically — it must be deliberately engineered. Service accounts that are granted administrator-level access for convenience during development and never scoped down in production create paths that attackers can exploit to move laterally across an entire cloud environment after gaining initial access to a single workload. In healthcare, where cloud environments often host both clinical applications and administrative systems, the blast radius of a compromised overpermissioned role can be catastrophic.
Unencrypted data at rest persists as a finding in healthcare cloud environments despite being among the most straightforward controls to implement. HIPAA’s encryption requirements are explicit, yet Wiz’s 2023 Cloud Security Report found that a significant percentage of cloud storage volumes in regulated industries remain unencrypted — often because encryption was not enabled during provisioning and no automated control caught the gap afterward.
Disabled or incomplete logging is particularly damaging in a post-breach context. CloudTrail, Azure Monitor, and GCP’s Cloud Audit Logs are the primary sources of forensic evidence after a cloud security incident. When these are disabled — frequently to reduce costs — organizations are left unable to determine what data was accessed, by whom, and for how long. From an OCR investigation perspective, the absence of audit logs is itself a HIPAA violation, compounding the original breach finding.
Exposed management interfaces — RDP and SSH ports open to the internet, cloud console access without MFA, administrative panels accessible from any IP — are a recurring finding in cloud penetration tests across industries. In healthcare cloud environments, these represent direct paths to systems containing PHI, exploitable through credential stuffing, brute force, or phishing without any need to compromise the application layer first.
Misconfigured network security groups and VPC rules allow traffic between cloud segments that should be isolated from one another. Clinical data systems should never be reachable from development environments, partner integrations, or internet-facing applications without explicit controls. When network rules are set broadly — allowing all inbound traffic on a port, or failing to segment PHI workloads from other cloud resources — the network provides no meaningful containment if another component is compromised.
Why Misconfiguration Is So Hard to Catch
Cloud environments are not static. They change constantly — new resources provisioned, new integrations added, configurations updated by multiple teams. A security baseline that was correct six months ago may have drifted significantly. A storage bucket created for a temporary data migration project that was never cleaned up. A security group rule added during an incident response engagement that was never revoked. An IAM policy attached to accommodate a vendor integration that was later replaced.
According to the NSA and CISA’s 2023 advisory on cloud security misconfigurations, the most dangerous configurations are frequently not the result of negligence — they are the result of legitimate operational activity that introduced risk without anyone recognizing it as such. This is why point-in-time audits are insufficient. Cloud environments require continuous visibility, not quarterly reviews.
What a Proactive Program Looks Like
Addressing cloud misconfiguration in a healthcare environment requires three capabilities working together.
The first is continuous attack surface monitoring. Every resource in the cloud environment — storage buckets, virtual machines, databases, serverless functions, IAM roles — needs to be inventoried and assessed against a security baseline on an ongoing basis. Changes that introduce risk need to be detected in near-real time, not at the next scheduled audit.
The second is penetration testing that explicitly targets the cloud environment. This means testing whether misconfigured resources are actually exploitable, whether network segmentation controls hold under attack conditions, and whether a compromised workload can reach PHI systems through overpermissioned IAM roles or misconfigured VPC rules. Static configuration review tells you what the settings are. Penetration testing tells you what an attacker can do with them.
The third is remediation validation. Fixing a misconfiguration is not the end of the process — it is the beginning of a verification cycle. Retesting to confirm that the fix was implemented correctly, that it did not introduce a new gap, and that the configuration has not drifted again is what separates a security program from a compliance checkbox exercise.
Key Takeaways for Security Leadership
Cloud misconfiguration is not a problem that gets solved once. It is an ongoing operational challenge that requires continuous attention, automated visibility, and regular adversarial testing. For healthcare organizations, the stakes are uniquely high: PHI exposure triggers regulatory consequences, patient trust erosion, and financial penalties that compound quickly.
The good news is that misconfiguration is also among the most preventable categories of cloud risk. Unlike a sophisticated zero-day exploit, a publicly exposed storage bucket or an overpermissioned IAM role can be identified, understood, and fixed. The challenge is knowing they exist in the first place — and having a program in place that ensures you find them before an attacker does.
Your cloud environment is part of your attack surface. It needs to be treated that way.
Want to understand what an attacker could do with your cloud environment today?Learn more at sprocketsecurity.com or reach out at contact@sprocketsecurity.com.


