Continuous Security Testing
Expert Driven Offensive Security Platform










































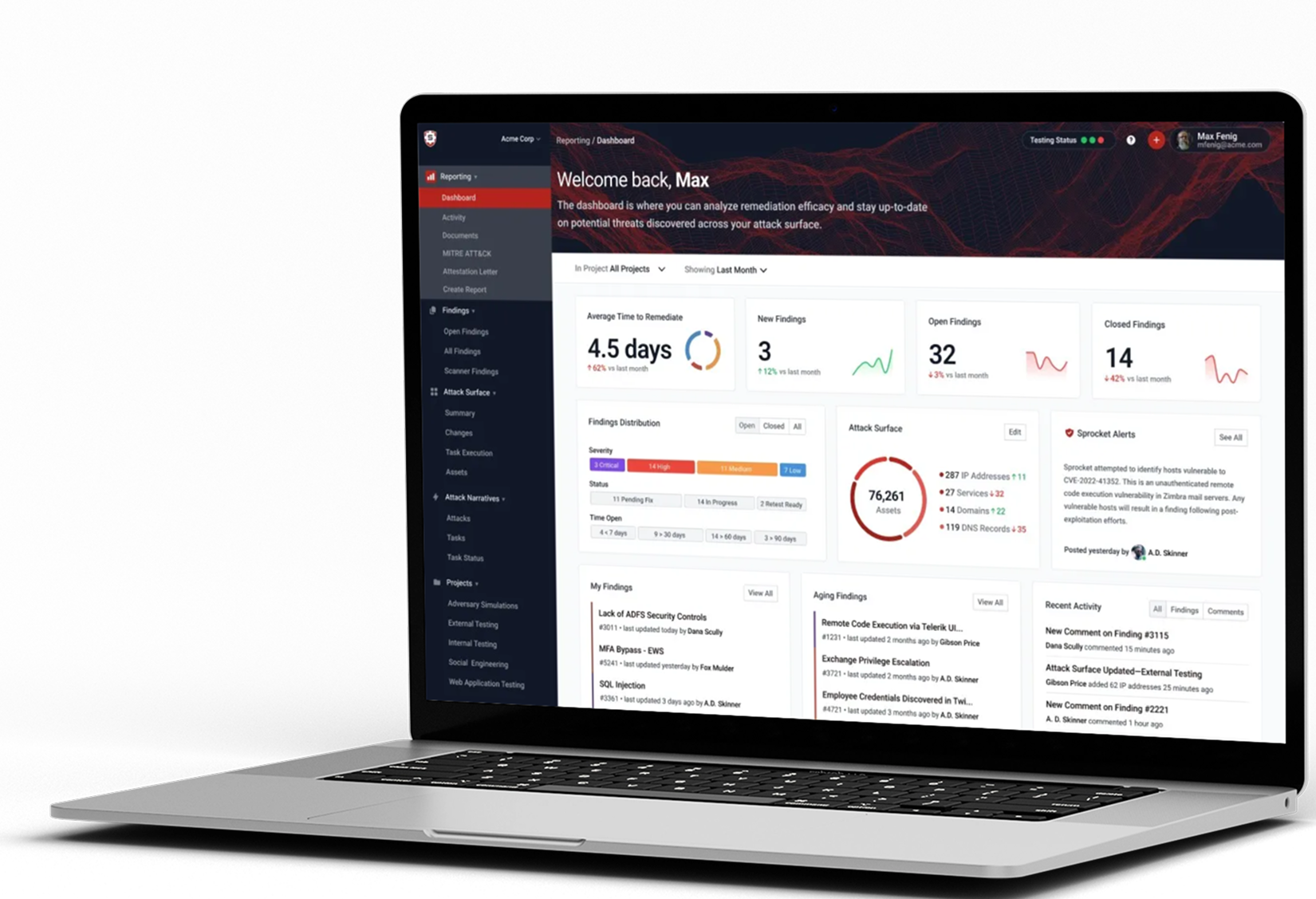
Platform
The Premier Offensive Security Platform
Identify and verify threats to your organization 24/7 from one platform.
Identify
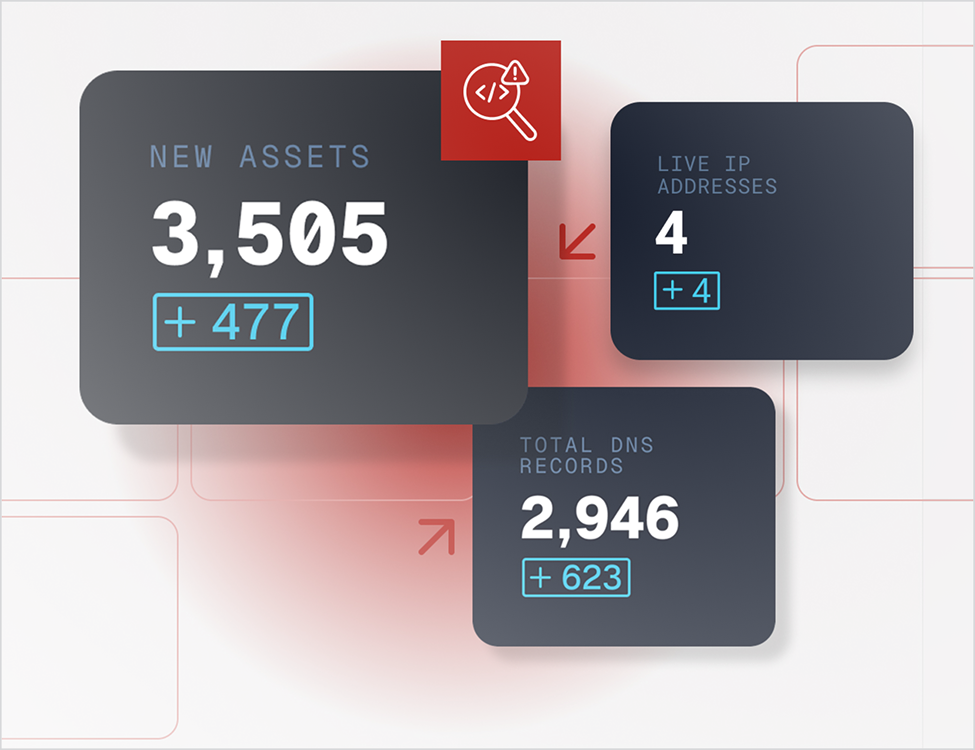
Attack Surface
Management
Management
Reveal the hackers' perspective of your organization's environment by the very same tools our experts use. Stay informed when your assets change or new threats are discovered. Manage all your IT infrastructure including hosts, services, domains, DNS records, websites, urls, emails, & usernames.
Verify
Continuous
Pentesting
Pentesting
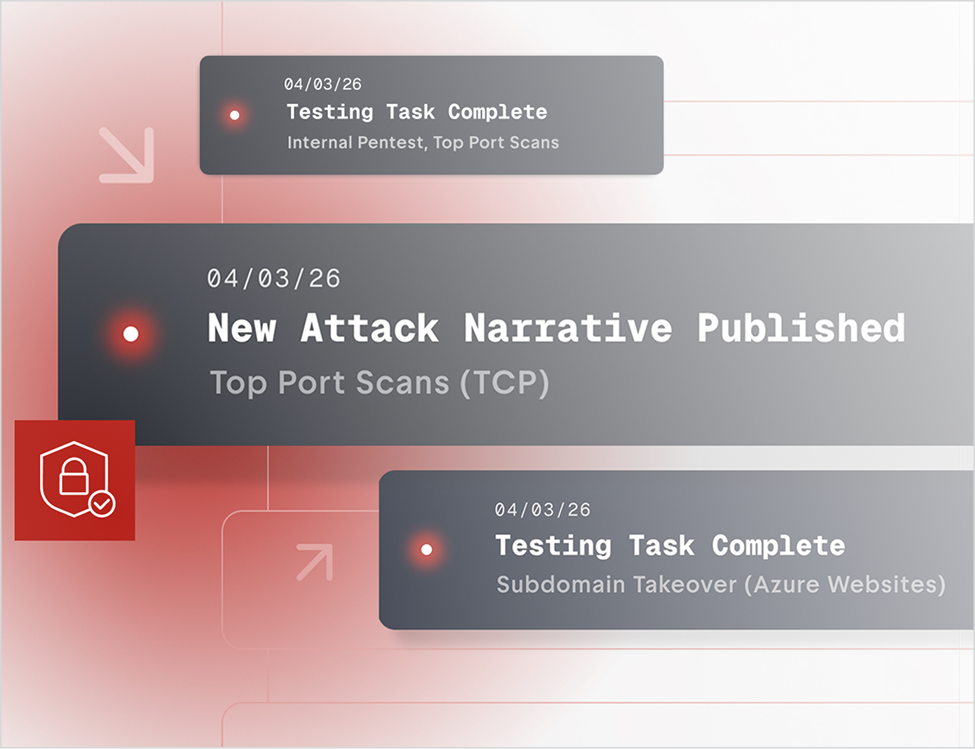
Remove the artificial time constraints on security tests. Attackers don't stop, and your assets and networks change throughout the year. Access unlimited retests, on-demand attestation reports, remain compliant, and get holistic security reporting with actionable insights.
Sprocket Blog
Explore Latest Resources.
 Can We Beat the Adversary, or Am I Willing to Accept the Risk?
Can We Beat the Adversary, or Am I Willing to Accept the Risk?
Most security programs detect breaches. Fewer can prove they won't happen. Learn the…
Security Budget Downturn
Budget cuts don't reduce security risk. They relocate it. Here's the breach math CFOs…
Hacking in the Age of AI: AI as the Attacker's Toolkit
If your adversaries are using AI to move faster, are you testing like they attack? Our…
The Human Touch in the Era of AI: Why Pentesting Still Needs a Human in the Loop
AI accelerates pentesting but human judgement close the gap. See how two real engagements…