Simulate:
Adversary Simulations
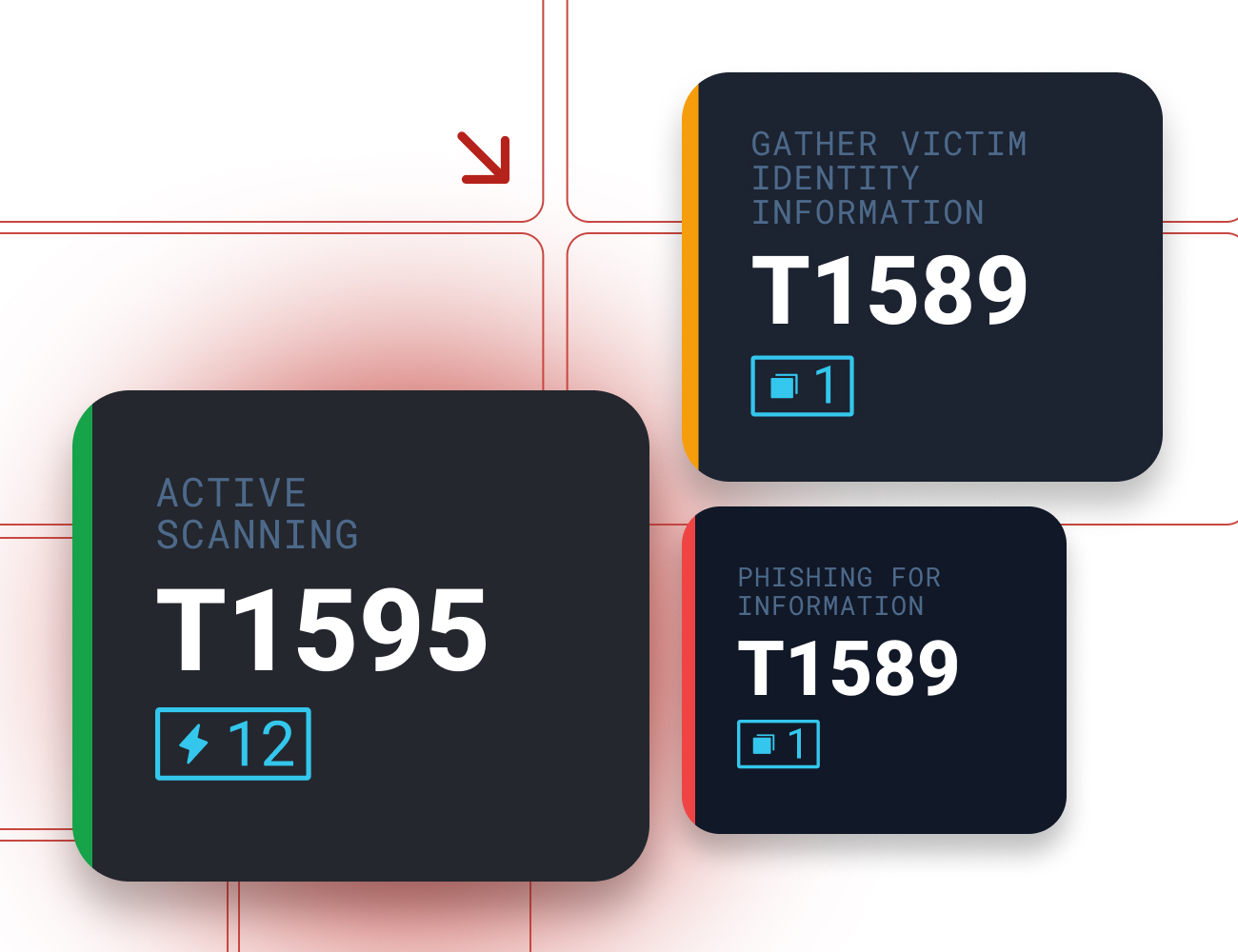
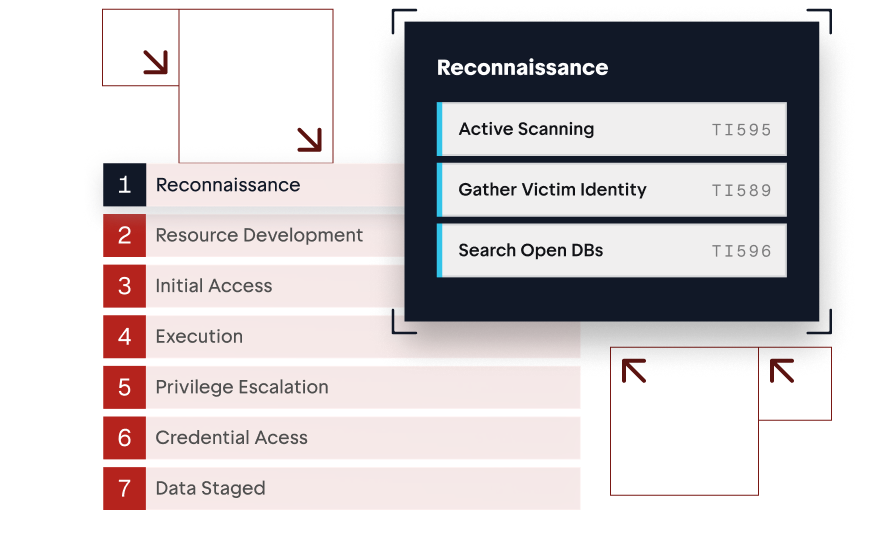
Emulate skilled opponents using bleeding edge techniques across complex attack paths with purple teaming, scenario driven, & MITRE ATT&CK.
Use Cases
Emulate real-world attacks to strengthen security against bleeding-edge threats.
Purple Teaming
Collaborative validation and remediation.
Your security team works directly with Sprocket testers to validate detections, tune controls, and retest continuously with rapid feedback loops.
Scenario-Driven Testing
Threats tested as they emerge.
Designed attack scenarios mirror active real-world threats so vulnerabilities are identified when risk is highest, not after an incident.
SecOps Enablement
Continuous visibility for security operations.
Maintain compliance and strengthen incident response with a real-time view of threats actively affecting your network.
Threat Intelligence Testing
Adversary-informed security validation.
Current threat intelligence is translated into live testing against your environment to improve situational awareness and risk-based decisions.
Control Tuning
Defenses optimized against real attack techniques.
Weak points in your security stack are identified and tuned using the exact techniques posing the greatest risk to your organization.
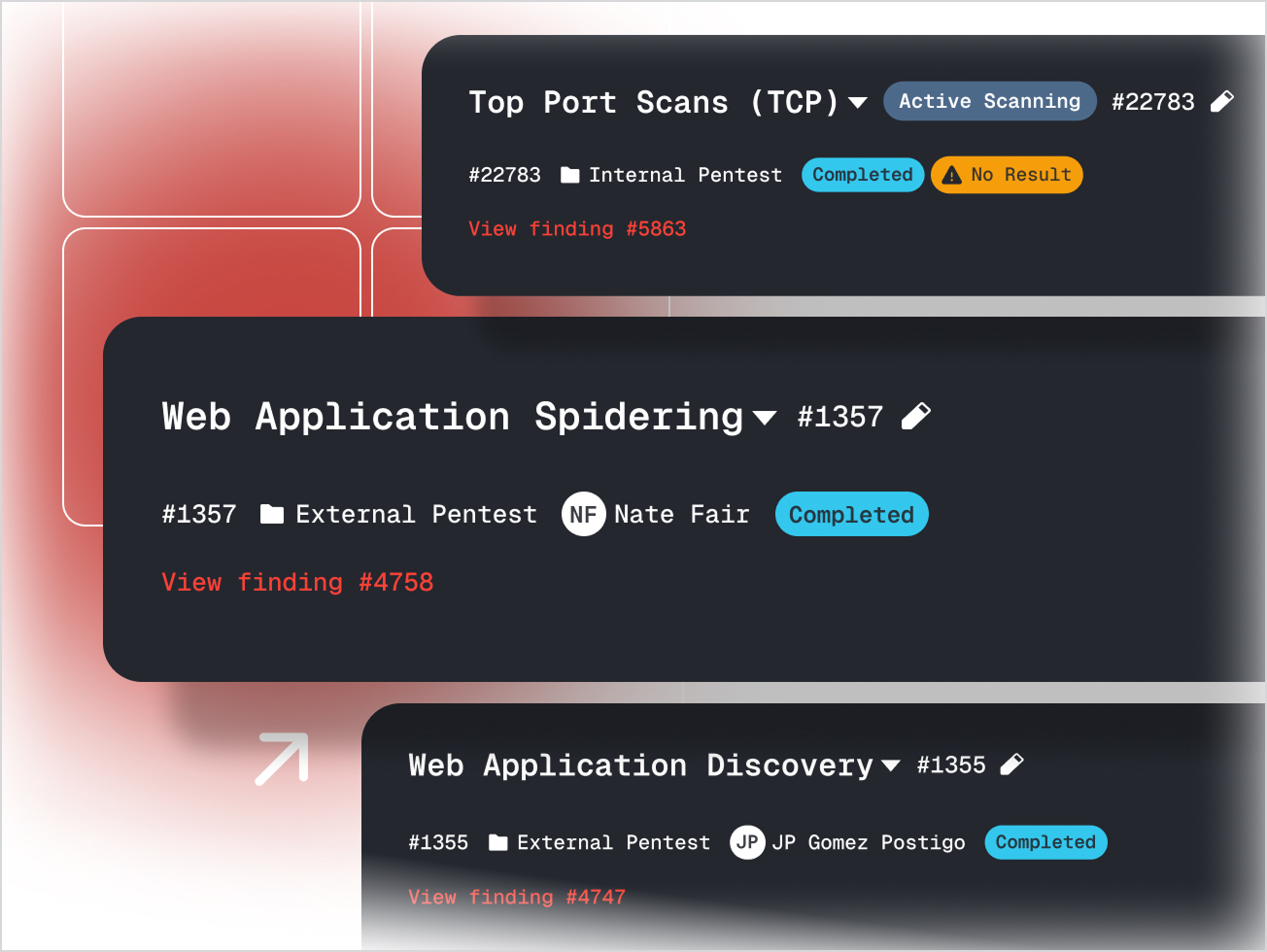
See the Sprocket Platform in Action
See the Sprocket Platform in action with a short demo that connects discovery, testing, reporting, and compliance in one dashboard. Watch how exposures are validated, guidance delivered, and compliance evidence generated — showing exactly how Sprocket keeps you ahead of attackers.
In this Demo You'll See:
Explore Latest Resources.
 Ahead of the Breach - Gary Lobermier, Lead Adversarial Security Engineer at Northwestern Mutual
Ahead of the Breach - Gary Lobermier, Lead Adversarial Security Engineer at Northwestern Mutual
Gary Lobermier of Northwestern Mutual on building purple team automation that validates…
Discover how a self-propagating XSS worm exploits multi-tenant widget frameworks to…
MFA doesn't stop session cookie replay. Endpoint detection doesn't catch fileless malware…
Step-by-step walkthrough of cracking NTLMv1-SSP hashes with rainbow tables, including how…