The Sprocket Platform:
Continuous Offensive Security
One platform combining continuous attack surface discovery, real-time exploit validation and human driven testing — all built to help you stay ahead of the attackers.

Why Point-in-Time Testing Fails
Pentesting is painful. It’s hard to schedule, communication is slow, and the results are outdated fast. Staying secure, and compliant, should not depend on once-a-year testing.

"Doing pentests is hard"
Traditional penetration tests are harder than they should be. Scheduling takes weeks, results are outdated by the time they are delivered, and they miss constant changes in your environment.

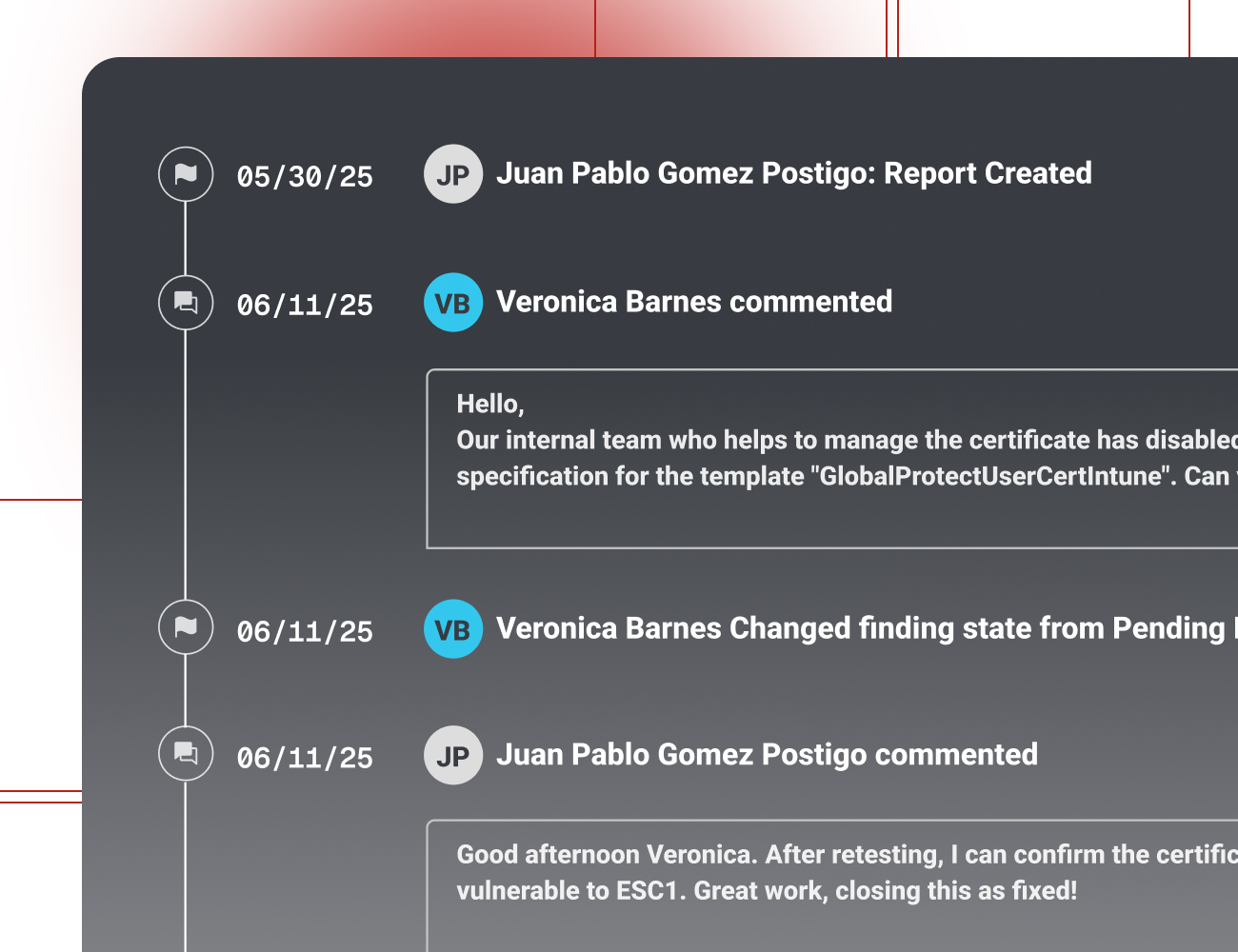
"Communication is slow and fragmented"
Communication with your vendor can be slow, leaving your team waiting for weeks with little visibility into progress or findings. Then when moving into remediation, there can be delays as testers move on leaving you exposed.

"Falling out of compliance between tests"
It’s tough to meet framework standards when your penetration tests only happen once or twice a year. Point-in-time reports quickly become outdated, leaving gaps auditors notice and attackers can exploit.
What We Test
Your attack surface goes far beyond the public internet. Sprocket’s team provides specialized testing across every critical environment as part of your Continuous Testing program.
External Penetration Testing
The foundation of your exposure-based threat validation.
Our team continuously tests your internet-facing assets, including domains, applications, APIs, and cloud services, to uncover real-world exploitable risks and forgotten attack paths.
Go to External Testing →
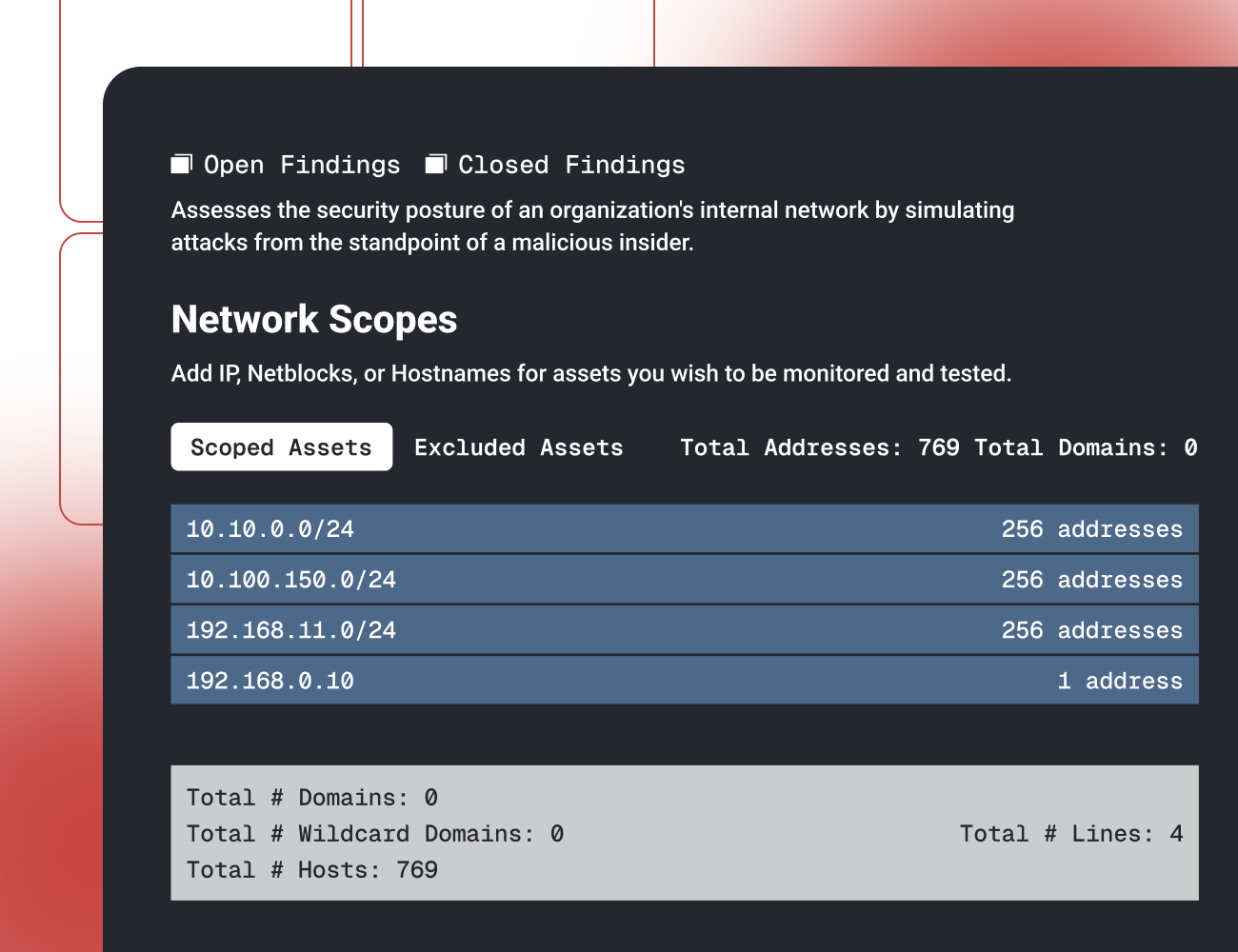
Internal Penetration Testing
Uncover how attackers move once inside.
Our testers simulate insider threats and post-breach behavior by moving laterally, escalating privileges, and targeting your most critical internal systems and infrastructure.
Go to Internal Testing →
Social Engineering
Test the human layer of your security program.
We assess employee susceptibility through controlled phishing, vishing, and social engineering campaigns to validate security awareness and response effectiveness.
Go to Social Engineering →
Web Application Testing
Continuously validate application-layer security.
Our experts test modern web applications against real-world attack techniques to identify vulnerabilities before they turn into breaches.
Go to Web App Testing →
See the Sprocket Platform in Action
See the Sprocket Platform in action with a short demo that connects discovery, testing, reporting, and compliance in one dashboard. Watch how exposures are validated, guidance delivered, and compliance evidence generated — showing exactly how Sprocket keeps you ahead of attackers.
In this Demo You'll See:
Explore Latest Resources.
 Hook, Line, and Server
Hook, Line, and Server
MFA doesn't stop session cookie replay. Endpoint detection doesn't catch fileless malware…
Step-by-step walkthrough of cracking NTLMv1-SSP hashes with rainbow tables, including how…
Discover how an unsanitized file write endpoint in Omega Enterprise Gateway escalates to…
Legacy healthcare systems can’t be patched but they can’t be ignored. Learn how to…