Ransomware doesn’t just lock files in healthcare. It stops care.
When a hospital’s systems go down, nurses revert to paper, imaging results can’t be retrieved, surgeries get delayed, and ambulances get diverted. In 2024, a cyberattack on Ascension Health forced staff across multiple states to disconnect clinical systems and hand-write medication orders for weeks. The technology meant to support patient care became the liability that threatened it.
For healthcare security leaders, the question is no longer whether ransomware will target your organization. It’s whether your security posture can limit how far an attacker gets once they’re inside.
Recovery within one week - healthcare ransomware victims
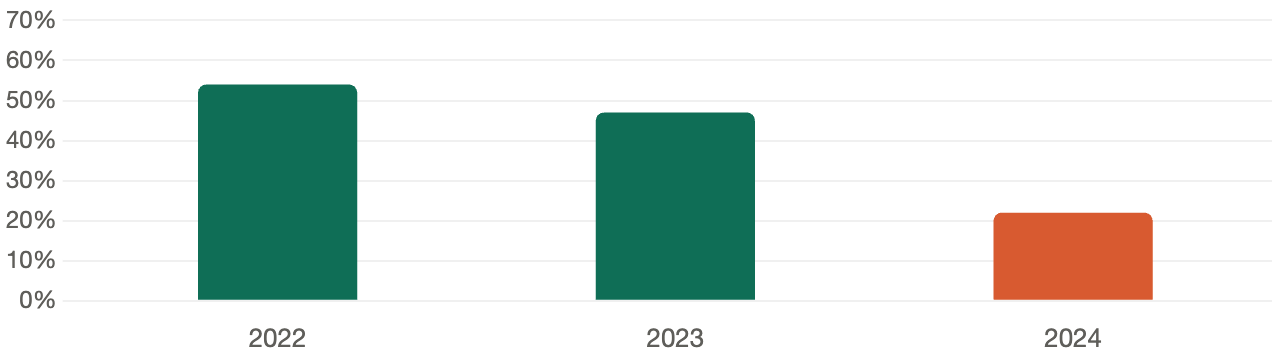 Sources: JumpCloud 2024 Ransomware Statistics; Sophos / DialogHealth Healthcare Cybersecurity Statistics 2025
Sources: JumpCloud 2024 Ransomware Statistics; Sophos / DialogHealth Healthcare Cybersecurity Statistics 2025The Annual Pentest Problem
Most healthcare organizations rely on annual penetration testing to validate their security controls. On paper, it seems reasonable: hire a firm, get a report, fix the findings, repeat next year.
In practice, it leaves you exposed for 345 days.
Over 19,000 critical and high severity vulnerabilities are published each year. The average time for attackers to exploit a newly disclosed vulnerability is just five days. Your annual test may have given you a clean bill of health in January, but by March, your environment has changed - new cloud services deployed, vendor access added, devices onboarded and none of it has been tested.
Ransomware actors know this. They don’t announce themselves. They move quietly through networks, identifying high-value targets, establishing persistence, and waiting. The average dwell time, the period between initial compromise and ransomware deployment, has historically ranged from days to weeks. Every untested day is an opportunity for an attacker to move deeper into your environment before you know they’re there.
What Attackers Are Actually Targeting
Healthcare is uniquely attractive to ransomware groups for two reasons: the sensitivity of the data and the operational urgency of the systems. Attackers know that a hospital under a ransomware attack cannot simply wait out a negotiation. Patient care creates leverage.
The attack vectors aren’t exotic. They’re the same misconfigurations, unpatched systems, and overlooked credentials that show up in penetration test reports across the industry. Exposed remote access services. Medical devices running outdated firmware sitting on insufficiently segmented networks. Third-party EHR integrations with excessive access. Legacy systems that can’t be patched but haven’t been compensating-controlled either.
According to the HHS Office for Civil Rights, hacking and IT incidents now account for the majority of large healthcare breaches and network server attacks represent the most common breach type. These aren’t sophisticated zero-day exploits. They’re known weaknesses that weren’t found and fixed before an attacker found them first.
Why Continuous Testing Changes the Equation
The fundamental problem with point-in-time testing is that your environment doesn’t stop changing when the test ends. New assets appear, configurations drift, and the threat landscape shifts. Continuous penetration testing is designed for that reality.
At Sprocket Security, the model works like this: attack surface monitoring runs persistently across your external environment, tracking domains, IP addresses, services, DNS records, and new assets as they appear. When something changes, it doesn’t just trigger an automated scan. It triggers a human. A credentialed penetration tester reviews the change and determines whether it warrants active testing. That’s the difference between knowing something new is on your perimeter and knowing whether it’s exploitable.
This matters enormously in healthcare, where IT environments are among the most complex in any industry. EHR integrations, connected medical devices, telehealth platforms, cloud migrations — each one represents a potential expansion of your attack surface. Under a continuous model, each one gets evaluated as it appears, not during next year’s scheduled engagement.
For ransomware specifically, the benefit is in shrinking the window. Ransomware requires an initial foothold, lateral movement, privilege escalation, and payload deployment. Each of those stages is an opportunity to detect and disrupt, but only if you know where your weaknesses are. Continuous testing finds and surfaces those weaknesses in near real-time, so your team can remediate before an attacker reaches the next stage.
From Detection to Remediation
Finding vulnerabilities is only useful if you can act on them. This is where many security programs stall. A report lands, findings get triaged, and remediation sits in a queue while teams debate severity ratings.
Sprocket’s platform is built to drive that process forward. Findings are published in real time, with full attack narratives that explain not just what was found, but how an attacker would use it. Remediation guidance is specific. Retesting is included - no scheduling, no additional cost. When your team fixes something, you can verify it immediately.
For healthcare security and compliance teams, the platform also generates on-demand attestation reports, which matters when auditors, board members, or cyber insurance carriers want evidence of your security program. Continuous testing doesn’t just improve your posture — it documents it.
What Decision Makers Should Be Asking
If you’re responsible for security, compliance, or operations in a healthcare organization, the right question isn’t whether you’ve been tested. It’s whether your testing keeps pace with how your environment and the threat landscape actually change.
A one-time assessment, however thorough, is a snapshot. Ransomware actors are working in real time. Your testing program should be too.
Healthcare organizations that have moved from annual testing to a continuous model report meaningful reductions in exposure time and faster remediation cycles — without adding headcount. For a small security team already stretched across compliance requirements, clinical operations, and vendor oversight, that matters.
Protecting patient care starts with knowing where your environment is vulnerable — not once a year, but continuously.


