There was a time when the security perimeter of a hospital meant a firewall at the edge of the network and VPN access for remote staff. That model is gone. Today, the average large hospital operates somewhere between 10,000 and 15,000 connected medical devices — infusion pumps, patient monitors, imaging systems, ventilators, nurse call stations — and the vast majority of them were never designed with security in mind. They run outdated operating systems, use default credentials that never get changed, and sit on networks alongside EHR systems holding the most sensitive data imaginable.
For attackers, that’s not a challenge. That’s an invitation.
The Scale of the Problem
“Medical devices are increasingly targeted by threat actors because they are high-value, often unmonitored, and rarely patched — a perfect combination for establishing persistent access inside a healthcare network.”
— HHS 405(d) Task Group, Health Industry Cybersecurity Practices, 2023
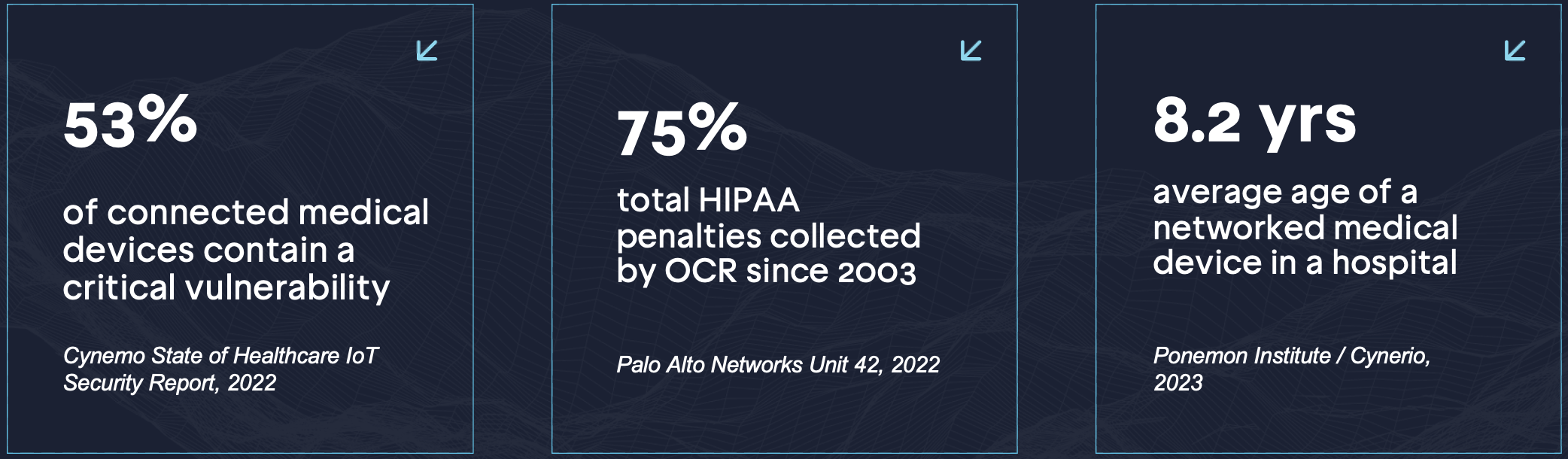
The research paints a stark picture. According to Cynerio’s State of Healthcare IoT Security Report, 53% of connected medical devices contain at least one critical vulnerability. Palo Alto Networks’ Unit 42 team found that 75% of infusion pumps — one of the most ubiquitous devices in any clinical setting — have known, unpatched security flaws. And the Ponemon Institute has documented that the average networked medical device in a hospital is 8.2 years old, meaning most predate modern security requirements and many run operating systems that no longer receive vendor support.
These aren’t abstract risks. In 2020, a ransomware attack on a German hospital was directly linked to a patient death after emergency care was diverted. In 2022, the FDA issued alerts about vulnerabilities in widely deployed infusion pump platforms that could allow remote code execution — not through a sophisticated zero-day, but through default credentials that had never been changed. In 2023, the HHS Office of Information Security published an advisory specifically warning that legacy medical devices were being used as pivot points in ransomware intrusions targeting patient records.
How an Attack Actually Unfolds
The threat isn’t hypothetical, and it doesn’t require a nation-state actor. The typical medical device compromise follows a predictable pattern that any competent attacker can execute.
It starts with reconnaissance. Tools like Shodan and Censys index internet-exposed medical devices in real time — including model numbers, firmware versions, and open ports. An attacker can identify a vulnerable infusion pump or patient monitor without ever touching the target network. From there, initial access is often trivially easy: default manufacturer credentials, a known CVE in aging firmware, or an unencrypted management interface exposed on the internal VLAN.
The critical moment comes next. Because medical devices almost never run endpoint detection software — you cannot install an EDR agent on a ventilator — there is no alert, no quarantine, no automated response. The attacker is on the network, invisible, and free to move. From the compromised device, they pivot to clinical workstations, target Active Directory, and begin working toward the EHR system or the backup infrastructure. By the time the intrusion is discovered, the dwell time is typically measured in weeks.
This attack chain maps directly to MITRE ATT&CK for ICS techniques documented in real-world healthcare intrusions. What makes it particularly dangerous is that the entry point — the medical device — generates no meaningful security telemetry. It doesn’t appear in your SIEM. It doesn’t trigger your vulnerability scanner in a meaningful way. And it almost certainly hasn’t been included in your penetration testing scope.
Why Traditional Security Tools Miss This
Most enterprise security programs are built around assets that can run agents: laptops, servers, cloud instances. Medical devices fall outside that model entirely. They are what the industry calls “unmanaged” or “OT” (operational technology) assets — and the gap in visibility they create is exactly what attackers exploit.
Vulnerability scanning tools often cannot safely scan medical devices without risking disruption to patient care. A scan that crashes a monitoring system or resets an infusion pump mid-treatment is not an acceptable outcome. This means most healthcare organizations have large portions of their network that are effectively invisible to their security stack — and they know it.
According to a 2023 survey by the Ponemon Institute, 88% of healthcare organizations experienced at least one cyberattack in the past year, and among those, attacks involving medical devices or connected health technology were the fastest-growing category. Yet only 20% of respondents said they had a mature program for assessing and managing medical device security.
“The medical device attack surface is growing faster than the security programs designed to protect it. Organizations that treat these devices as outside the scope of their security program are operating with a blind spot that adversaries actively exploit.”
— American Hospital Association, Cybersecurity Advisory, 2024
What a Proactive Program Looks Like
Closing this gap requires a different approach than traditional IT security. It starts with visibility — knowing every device on the network, its firmware version, its known vulnerabilities, and its network behavior. Attack surface management tools designed to safely discover and enumerate OT and IoT assets are the foundation.
From there, the security program needs to account for the reality that many of these devices cannot be patched on any reasonable timeline. Vendors may not release patches for years. Regulatory approval cycles for medical device software updates are long. In the interim, the answer is network segmentation — ensuring that a compromised infusion pump cannot reach the EHR system — combined with continuous monitoring for anomalous behavior on the device network segment.
Penetration testing for medical device environments requires specialists who understand both the clinical constraints and the attacker techniques. Testing cannot disrupt care, but it also cannot be so cautious that it fails to identify real attack paths. The goal is to map the realistic pivot paths an attacker would take from a compromised device and validate that the controls in place would detect and contain that movement before it reaches critical systems.
Critically, the scope of testing must include the device network — not just the enterprise IT environment. If your penetration testing program has never touched the VLAN where your infusion pumps and patient monitors live, you have not tested your perimeter. You have tested a smaller, safer version of it.
Key Takeaways for Security Leadership
Connected medical devices are no longer a niche concern at the edge of the IT security program. They are a primary attack surface — one that is growing, largely unmonitored, and increasingly targeted by ransomware operators and sophisticated threat actors alike.
The organizations best positioned to defend against this threat are those that have extended their security program to explicitly include medical devices: inventorying them, understanding their vulnerabilities, segmenting their networks, and testing the paths an attacker would actually take. That means attack surface monitoring that covers OT and IoT assets, penetration testing that includes the clinical device network, and continuous visibility into changes that might expose new risk.
The perimeter has moved. The question is whether your security program has moved with it.
Ready to extend your penetration testing program to include your medical device environment?Learn more at sprocketsecurity.com or reach out at contact@sprocketsecurity.com.


