Step-by-step walkthrough of cracking NTLMv1-SSP hashes with rainbow tables, including how to coerce auth, disable ESS, recover NT hashes, and remediate.
Resources
Blog
Testing Lab
Keep up to date with the latest offensive security news, knowledge, and resources.

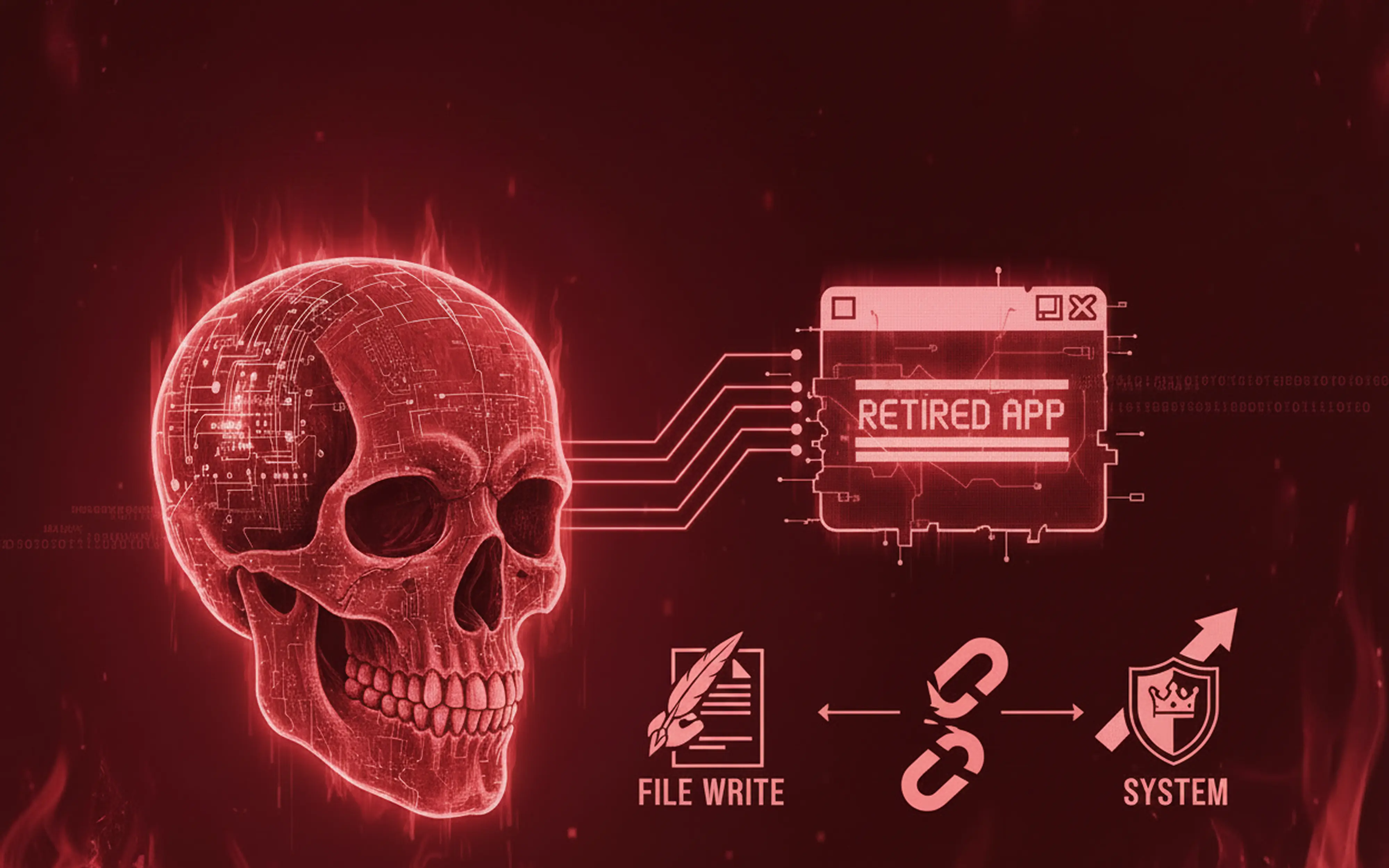
Discover how an unsanitized file write endpoint in Omega Enterprise Gateway escalates to SYSTEM-level code execution and what dead code reveals about real-world security bugs.
A successful prompt hack looks like your system working correctly for someone else. The mechanism that makes this possible is the same one you’re paying for.
The Axios supply chain attack exposed why dependency scanning fails against credential compromise. Learn how attackers backdoor popular packages and what your penetration tests are missing.
Multifunction printers silently store domain credentials, expose unauthenticated management interfaces, and sit on flat networks. Learn how attackers exploit MFPs to achieve domain admin in minutes.
Understanding how SiteGround’s proof-of-work CAPTCHA silently disrupts automated WordPress security scans and how to work around it.