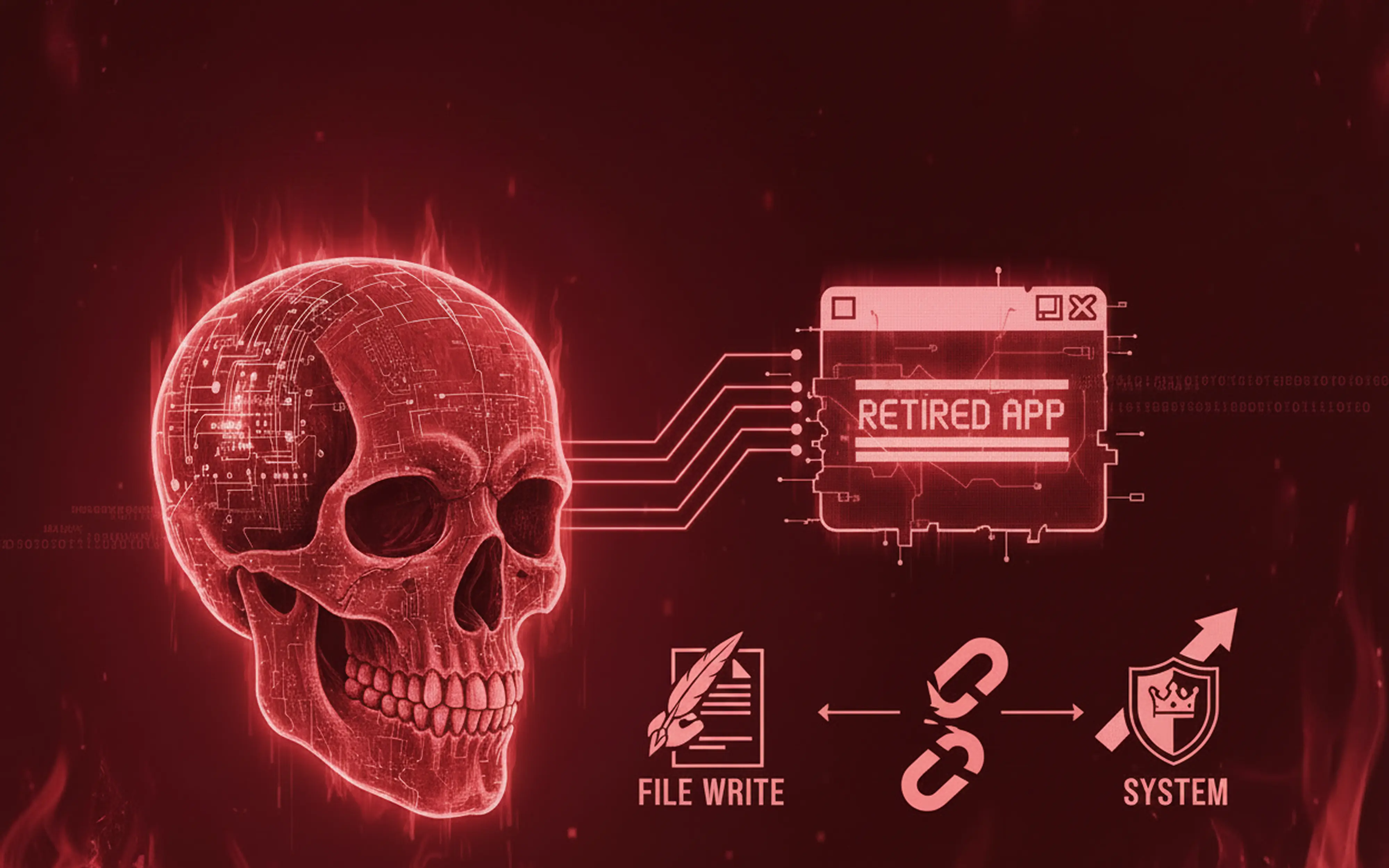
Discover how an unsanitized file write endpoint in Omega Enterprise Gateway escalates to SYSTEM-level code execution and what dead code reveals about real-world security bugs.
Resources
Blog
Nick Aures
Blogs by Nick Aures

Decompiling a retired .NET application reveals how a single middleware misconfiguration leads to full authentication bypass.
Nick Aures guides us through a real-life pentesting moment with important lessons for authentication using industry-standard technology, in this case JWTs.
Explore how Sprocket Security uncovered chained vulnerabilities and learn how overlooked parameters led to serious security risks.
Explore a security expert's take on validating the Next.js CVE-2025-29927 exploit, its impact, and techniques for assessing and mitigating the risk.