Discover how an unsanitized file write endpoint in Omega Enterprise Gateway escalates to SYSTEM-level code execution and what dead code reveals about real-world security bugs.
Resources
Blog
Vulnerability Analysis
Keep up to date with the latest offensive security news, knowledge, and resources.

Understanding how SiteGround’s proof-of-work CAPTCHA silently disrupts automated WordPress security scans and how to work around it.
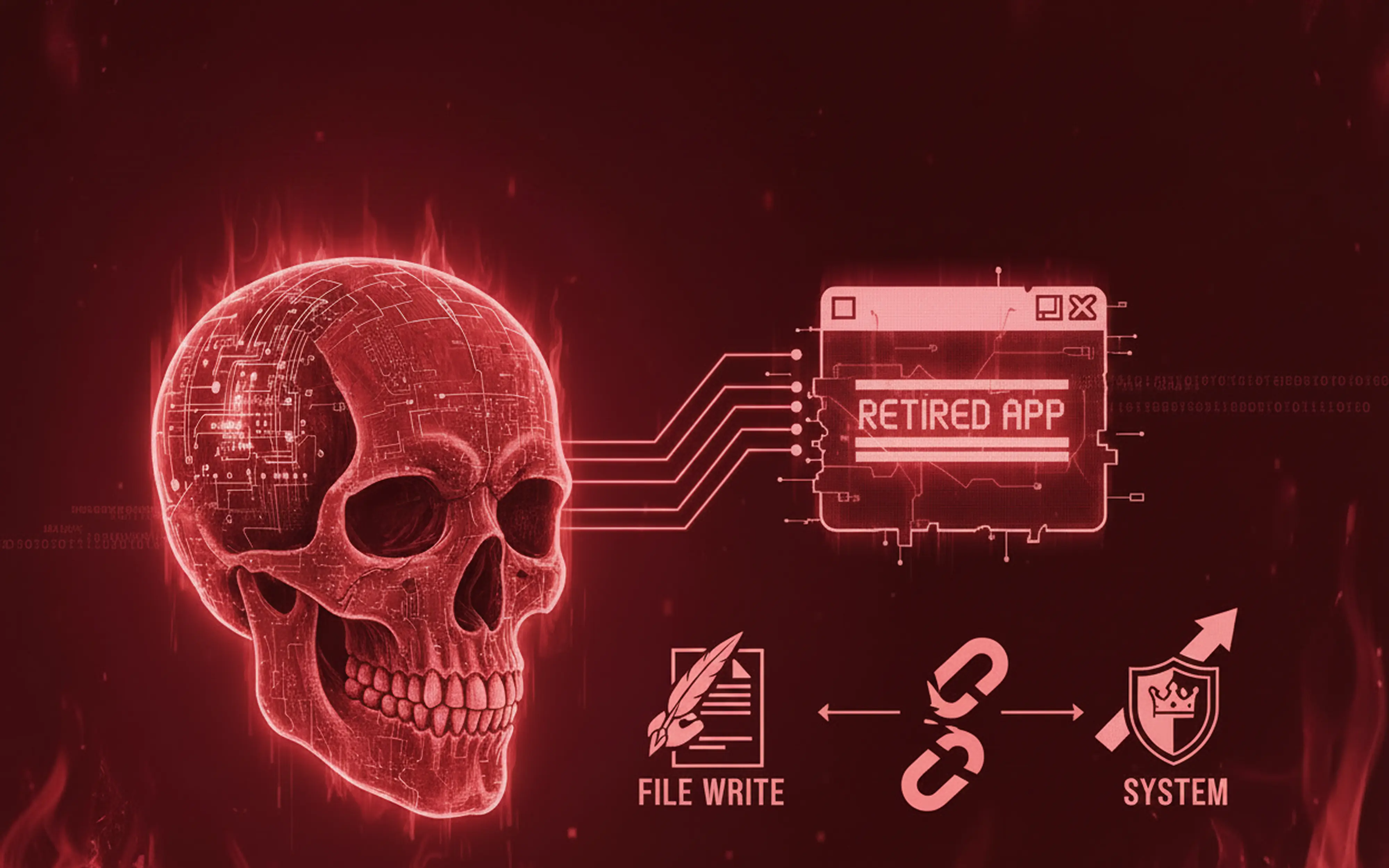
Decompiling a retired .NET application reveals how a single middleware misconfiguration leads to full authentication bypass.
Why traditional API pentests miss real commerce risk and how cart tokens, checkout flows, and cross-layer auth gaps expose customer data.
The vulnerability management lifecycle is a structured approach to managing potential security weaknesses in information systems.
Vulnerability testing is the process of identifying, assessing, and addressing security weaknesses in systems, networks, or applications