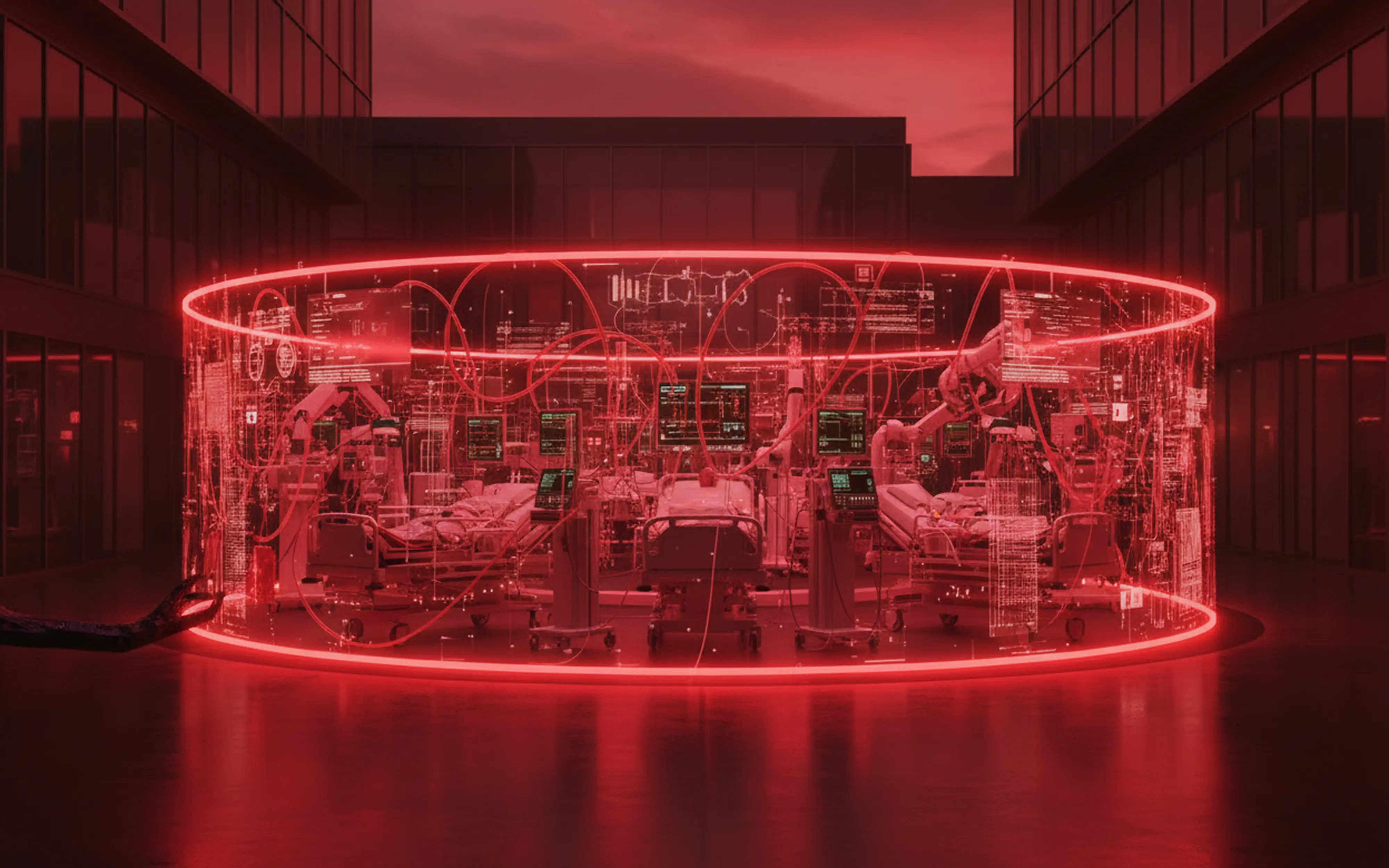
53% of connected medical devices have critical vulnerabilities. Learn how attackers and exploit IoT blind spots in healthcare networks and how to close them.
Resources
Blog
Strategic
Keep up to date with the latest offensive security news, knowledge, and resources.

Learn what HHS OCR investigators look for after a HIPAA breach and how continuous penetration testing builds the audit trail that proves your security programs works.
Healthcare ransomware exploits the gap between tests. See how continuous penetration testing reduces exposure, speeds remediation, and protects patient care.
Learn what DORA’s TLPT assessment requires, why most organizations fail on preparation (not vulnerabilities), and how to build a TLPT-ready security program.
87% of financial sector breaches involve a human element. Discover how deepfakes, spear-phishing, and pretexting are evolving and what leaders should test.
Cloud migrations create new attack vectors security teams aren’t testing. Learn how these expand your exposure and how to close the gaps.