You approved the cloud migration to cut costs, increase agility, and modernize infrastructure. The business case was solid. The timeline looked manageable. And now, six months in, your security team is watching the attack surface grow in ways that weren't in the original project plan.
This is not a hypothetical. It's the story playing out in organizations across every industry right now. Cloud migrations don't just move your infrastructure — they fundamentally reshape the way attackers see your organization. And if your security testing program is still built around annual assessments and a static list of known assets, you have a serious problem.
This post breaks down exactly how cloud migrations expand your attack surface, what the data says about attacker behavior, and what security leaders can do to stay ahead of exposures that appear the moment a new workload goes live.
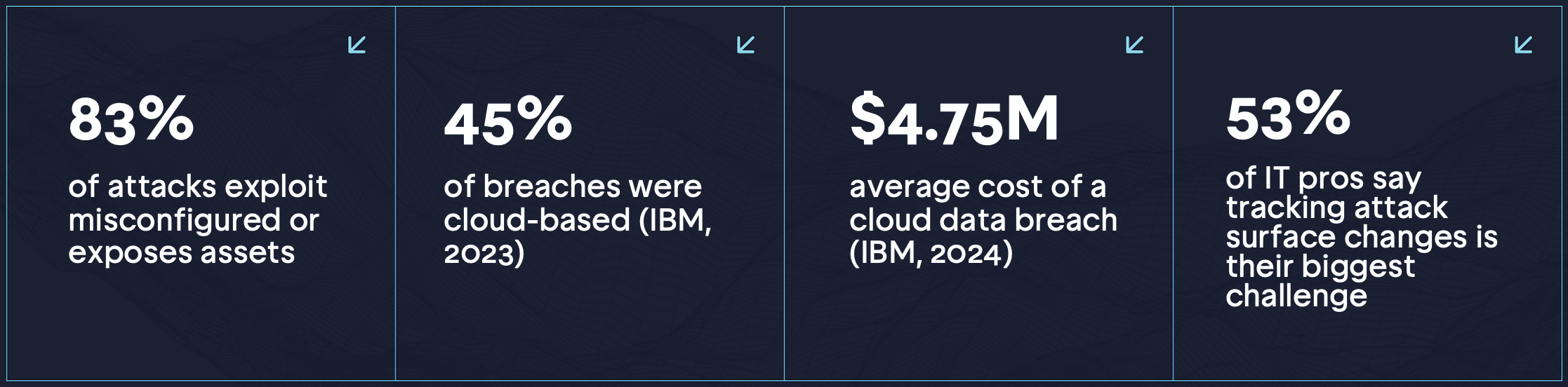 Sources: IBM Cost of a Data Breach Report 2023/2024; Sprocket Security ASM Data
Sources: IBM Cost of a Data Breach Report 2023/2024; Sprocket Security ASM DataThe Problem with How Most Organizations Think About Cloud Security
There is a common assumption in enterprise security: if you tested it before the migration, you’ve checked the box. The problem is that the moment workloads move to the cloud, the asset inventory that your last pentest was based on is already obsolete.
Cloud environments are dynamic by design. Auto-scaling spins up new instances. Developers provision S3 buckets, Azure blobs, and Lambda functions without going through formal IT channels. APIs get deployed and forgotten. Subdomains get created for testing and never decommissioned. Each one of these represents a new attack vector that didn’t exist when you completed your last assessment.
“Misconfigured cloud resources, subdomain takeovers, and forgotten assets can expose your entire organization to opportunistic and targeted attackers.” — Sprocket Security External Penetration Testing Overview
The 2024 Verizon Data Breach Investigations Report found that system intrusion, social engineering, and basic web application attacks account for the vast majority of breaches — and cloud assets have become a primary target for all three categories. When the perimeter disappears, so does the illusion of a fixed, testable scope.
What Changes When You Migrate to the Cloud
Understanding exactly how the attack surface expands during a cloud migration is the first step toward managing it. Here are the most significant shifts security leaders need to account for:
The Perimeter Becomes Elastic — and Invisible
On-premises environments have a defined perimeter: your firewall, your IP ranges, your data center. Cloud environments have no such boundary. Resources are provisioned programmatically, often without security team involvement. According to Gartner, through 2025, 99% of cloud security failures are expected to be the customer’s fault and the most common failure mode is misconfiguration.
Identity Becomes the New Perimeter — and It’s Frequently Misconfigured
In a cloud-first environment, Identity and Access Management (IAM) is the primary access control. The 2024 CrowdStrike Global Threat Report found that 80% of all cyberattacks now use identity-based techniques. Overly permissive IAM roles, publicly exposed service accounts, and hard-coded credentials in code repositories are among the most common cloud vulnerabilities Sprocket’s testers exploit during engagements — and they’re almost never on the asset list from the last annual pentest.
Shadow IT Explodes
Cloud services are frictionless by design. A developer can spin up a new EC2 instance, expose a web service, or create a public S3 bucket in minutes, without submitting a ticket. A 2024 Flexera State of the Cloud report found that 32% of cloud spending is wasted on unmanaged or unoptimized resources — a figure that also maps directly to assets that security teams have no visibility into.
Attack Surface Changes Daily — Not Annually
The average organization’s cloud environment changes significantly every single day. New containers, new microservices, new API endpoints — all of them representing potential attack vectors. The annual penetration test, which was already a blunt instrument for on-premises infrastructure, is essentially useless for validating the security posture of a dynamic cloud environment.
According to the 2024 IBM Cost of a Data Breach Report, the average time to identify a breach in cloud environments was 194 days. That’s over six months of exposure before detection. For organizations running annual pentests, the math gets grim quickly: if your test happened in January and a misconfigured cloud resource appeared in February, you’ve potentially been exposed for over a year before you find out.
Traditional Testing vs. Cloud Migration Reality
The table below illustrates how the assumptions built into legacy testing programs no longer hold in a cloud environment:
Traditional On-Prem Testing | Cloud Migration Reality |
|---|---|
Fixed perimeter — known IP ranges | Elastic IPs, ephemeral containers, serverless |
Annual scope rarely changes | Daily deployments add new assets continuously |
Physical access controls enforced | IAM misconfig = anyone from anywhere |
Shadow IT is rare | Developers spin up cloud resources without IT |
Compliance maps to known assets | Shared responsibility model creates gaps |
The Specific Risks That Show Up in Cloud Migrations
Sprocket’s pentesters see the same categories of cloud-migration exposures emerge across engagements with mid-market and enterprise organizations. These are the issues that annual tests miss — and attackers don’t.
S3 Bucket and Cloud Storage Misconfigurations
Public cloud storage misconfigurations remain one of the most common cloud security failures. In Sprocket’s sample engagements, testers have identified AWS S3 bucket takeover vulnerabilities where a domain pointed to a bucket that no longer existed allowing attackers to register the bucket and host malicious content on a trusted domain. The downstream impact includes phishing pages served from legitimate infrastructure, malware delivery, and supply chain compromise.
Real Finding from a Sprocket Engagement: An AWS S3 bucket associated with a customer subdomain was identified as vulnerable to takeover. The bucket had been deprovisioned during a cloud migration but the DNS record remained, allowing any external attacker to claim the bucket and serve malicious content on a trusted corporate domain.
Subdomain Takeovers
Subdomain takeovers are among the most underestimated cloud migration risks. As organizations move workloads to cloud providers and then decommission or change services, DNS records often lag behind. A CNAME pointing to an Azure Virtual Machine that has been terminated can be claimed by an attacker within hours of deprovisioning. The 2023 Detectify State of External Attack Surface report found that subdomain takeover vulnerabilities had increased by over 40% year-over-year, driven almost entirely by cloud resource churn.
Secrets and Credential Exposure
Cloud migrations frequently accelerate development velocity, which often means credentials and API keys end up in code repositories, Postman collections, CI/CD pipelines, and container images. A 2023 GitGuardian report found that secrets exposure in public GitHub repositories grew 67% year-over-year, and private repositories are not immune. Sprocket regularly identifies hardcoded credentials and exposed API keys during cloud-focused engagements.
Inherited Vulnerabilities from M&A and Acquired Infrastructure
Cloud migrations often coincide with M&A activity, where organizations are absorbing infrastructure they’ve never tested. Acquired cloud environments frequently carry years of technical debt: abandoned subdomains, public-facing development environments, unpatched services, and overly permissive IAM configurations. Security leaders have no visibility into what they’ve inherited until someone maps it.
Why Annual Testing Fails in Cloud Environments
The core problem with point-in-time penetration testing in a cloud environment is not the quality of the test itself — it’s the permanence assumption. Annual testing assumes that the scope you defined in January is still relevant in December. In cloud environments, that assumption fails before the final report is delivered.
Sprocket’s research found that on average, organizations’ external attack surfaces change meaningfully within 30 days of a penetration test — new assets appear, services are modified, and cloud resources are provisioned outside any formal change management process. This means that by the time a typical pentest report arrives as a PDF, it’s already describing an environment that no longer exists.
The problem compounds in cloud environments because the risk isn’t just from new assets — it’s from the pace of change itself. Attackers specifically target recently modified infrastructure. Known CVEs are weaponized within hours of disclosure. A newly deployed API endpoint can be discovered and exploited within days. The 345-day gap between annual tests is not a planning abstraction, it is a real attack window.
What Security Leaders Should Do About It
Addressing cloud migration attack surface expansion requires a fundamental shift in how security testing is scoped, scheduled, and sustained. Here are the actions security leaders should prioritize:
- Map your actual attack surface before and during migration. You cannot protect what you cannot see. Use Attack Surface Management (ASM) tooling to continuously enumerate your external footprint, domains, subdomains, IP addresses, APIs, and cloud services, from an attacker’s perspective.
- Treat cloud change events as testing triggers. Every significant infrastructure change: a new cloud workload, a new API, a DNS change, a new deployment, should trigger a security assessment of the changed components. Waiting for the next annual cycle is not a viable option.
- Validate IAM configurations continuously. Misconfigured IAM roles and over-permissioned service accounts are among the highest-risk exposures in cloud environments. Regular validation against least-privilege principles should be built into the cloud operations workflow.
- Decommission DNS records immediately when cloud resources are retired. S3 buckets, Azure VMs, and other cloud resources should have their associated DNS records removed simultaneously. Stale DNS is one of the easiest attack vectors to prevent and one of the most commonly overlooked.
- Include inherited infrastructure in scope immediately. M&A activity should trigger immediate attack surface enumeration of acquired environments, not after integration is complete. Attackers will not wait.
- Move from periodic to continuous penetration testing. The only way to validate security posture in a dynamic cloud environment is to test continuously, not annually. This means coverage that automatically adjusts to infrastructure changes, with expert human validation of every critical finding.
How Sprocket Security Addresses Cloud Migration Exposure
Sprocket Security was built specifically for environments that change faster than annual testing can track. The platform continuously monitors your external attack surface using the same reconnaissance techniques attackers use — DNS enumeration, subdomain brute-forcing, port scanning, and cloud asset discovery and automatically triggers expert-driven penetration testing when something changes.
When a new cloud asset appears in your environment, Sprocket’s ASM engine surfaces it immediately. When a critical finding is identified, a US-based expert tester validates exploitability before it’s surfaced to your team eliminating the noise that slows down remediation. And when a fix is deployed, unlimited retesting confirms the exposure is actually closed.
For organizations undergoing cloud migrations, this means you get continuous visibility into the attack surface you’re building, not a snapshot of the one you had. Security leadership gets always-current reporting for compliance and board communications. And your security team spends time on real exploitable findings, not chasing scanner noise.
Sprocket also offers a free Attack Surface Management (ASM) Community Edition that gives organizations immediate, attacker-perspective visibility into their external footprint at no cost — making it a practical first step for any team beginning a cloud migration.
The Bottom Line
Cloud migrations create real, material security exposure. The data is clear: cloud-based breaches are rising, misconfiguration is the leading cause, and the speed of change in cloud environments has rendered point-in-time testing obsolete as a primary security assurance mechanism.
Security leaders who are navigating cloud migrations need to answer one question honestly: is your current testing program actually keeping pace with the environment it’s supposed to protect? If the answer is no or “I’m not sure” - that gap is exactly what attackers are counting on.
See Your Attack Surface the Way Attackers Do
Start with Sprocket’s free Attack Surface Management platform - no cost, no commitment. Get immediate visibility into your external exposure and understand what your cloud migration has created before attackers find it first.
START FREE → sprocketsecurity.com/products/attack-surface-management
Citations & References
- IBM Security. (2024). Cost of a Data Breach Report 2024. IBM Corporation.
- IBM Security. (2023). Cost of a Data Breach Report 2023. IBM Corporation.
- Verizon. (2024). 2024 Data Breach Investigations Report. Verizon Business.
- CrowdStrike. (2024). 2024 Global Threat Report. CrowdStrike Holdings.
- Gartner. (2023). Is the Cloud Secure? Gartner Research. ID: G00757741.
- Flexera. (2024). 2024 State of the Cloud Report. Flexera Software LLC.
- GitGuardian. (2023). 2023 State of Secrets Sprawl Report. GitGuardian.
- Detectify. (2023). State of External Attack Surface Security. Detectify AB.
- Sprocket Security. (2025). ASM Product Data and Engagement Research. Sprocket Security, Inc.
- Sprocket Security. (2026). 2026 Messaging Framework. Internal Research. Sprocket Security, Inc.

