Every ransomware postmortem asks the same question: how did attackers get in? The better question, the one that actually determines your outcome, is how long were they already inside before anyone noticed.
Ransomware is not a single event. It is the final act of a campaign that began weeks, sometimes months, before an encryption payload ever executes. By the time the ransom note appears on your screens, the attacker has mapped your network, exfiltrated your data, compromised your backups, and positioned themselves for maximum damage. The variable that separates a contained incident from an operational catastrophe is dwell time and most organizations are getting it catastrophically wrong.
For security leaders whose boards are asking about ransomware risk, the conversation needs to shift away from "are we protected?" and toward "how quickly would we know?" Those are fundamentally different questions, and the second one has a measurable answer.
What Is Dwell Time, and Why Does It Define Your Blast Radius?
Dwell time is the period between initial compromise and detection - the window during which attackers operate freely inside your environment. Every hour that window stays open is an hour of reconnaissance, lateral movement, privilege escalation, and data staging. It is the variable attackers deliberately maximize, and that defenders consistently underestimate.
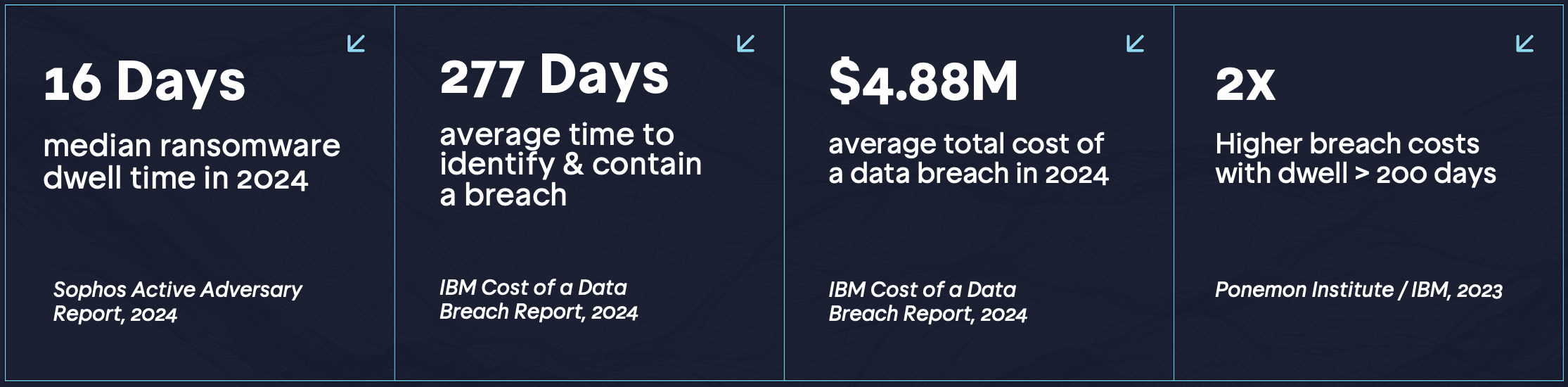
The numbers are damning. The median dwell time for ransomware attacks tracked by Sophos in 2024 was 16 days, but that is the median. Many incidents see attackers persist for months undetected. The Mandiant M-Trends 2024 report found a global median detection time of 10 days across all intrusion types, but noted that ransomware actors with longer dwell times consistently inflicted greater financial and operational damage. The correlation is direct: more time inside equals a larger blast radius.
Attackers don't clock out. They operate continuously, learning your environment while your team is watching dashboards that reflect last quarter's state.
What Attackers Actually Do During Dwell Time
Understanding dwell time as a risk variable requires understanding what adversaries accomplish during it. This is not idle time — it is systematic preparation for maximum impact.
RANSOMWARE KILL CHAIN — WHAT'S HAPPENING INSIDE YOUR NETWORK
| Day 1 | Initial Access Attacker gains foothold via phishing, exposed VPN credential, unpatched external service, or purchased access from an Initial Access Broker (IAB). No alert. No indication anything is wrong.
| Days 2–5 | Reconnaissance & Lateral Movement Internal network mapping, Active Directory enumeration, credential harvesting. The attacker identifies high-value targets: finance servers, backup infrastructure, domain controllers.
| Days 6–12 | Privilege Escalation & Persistence Domain Admin access achieved. Backdoors and remote access tools installed across multiple hosts. Backup systems are identified and targeted for deletion or encryption first.
| Days 13–15 | Data Exfiltration Sensitive data exfiltrated to attacker-controlled infrastructure — intellectual property, PII, financial records, M&A documents. This enables double-extortion: pay or data gets published.
| Day 16+ | Ransomware Deployment Payload detonated across all compromised hosts simultaneously. Backups are already gone. The ransom note appears. By this point, the damage is done — encryption is the announcement, not the attack.
The Coveware Q4 2024 Ransomware Marketplace Report confirmed that double-extortion attacks — where data is stolen before encryption — now represent the majority of ransomware incidents. [4] This means that even organizations with robust backup infrastructure cannot simply restore their way out of a long-dwell intrusion. The data was already gone before the ransom note appeared.
Why You Don't Know They're There
The uncomfortable truth is that most organizations lack the visibility to detect an attacker operating inside their environment with legitimate-looking credentials and tools. Modern ransomware actors practice "living off the land" — they use built-in Windows utilities, legitimate remote management tools, and valid stolen credentials to blend into normal traffic patterns. Your SIEM sees the noise; it does not necessarily see the threat.
According to Verizon's 2024 Data Breach Investigations Report, 77% of web application attacks involved use of stolen credentials. [5] An attacker operating with a valid domain administrator account looks exactly like a domain administrator. Detection requires behavioral understanding of what that account normally does — a capability most mid-market organizations have not operationalized.
THE EXPOSURE WINDOW PROBLEM
Annual Testing Creates a 364-Day Blind Spot
Most organizations run a penetration test once a year. That test reflects their security posture on one specific day. Between that day and the next test, infrastructure changes, new vulnerabilities emerge, cloud assets drift, development teams push code, and employees click things they shouldn't. Every one of those changes is an unverified exposure. Attackers know this. They target the gaps between your tests, not the day of them.
The Access Broker Economy Is Accelerating This Problem
One factor security leaders often under appreciate is the industrialization of initial access. Initial Access Brokers (IABs) are threat actors who specialize in compromising organizations and then selling that access to ransomware operators via dark web marketplaces. This creates an ecosystem where your environment may already be compromised and listed for sale before a ransomware group has even begun targeting you.
Recorded Future's 2024 Annual Report on Ransomware documented over 5,000 organizations publicly named by ransomware leak sites — a 15% increase from 2023. [6] The underground economy supporting these attacks is mature, efficient, and growing. An organization that tests its external perimeter annually and considers itself assessed is operating on an assumption that the threat landscape waits for their schedule. It does not.
This is precisely why attack surface management is no longer optional infrastructure. If you cannot see your externally exposed assets continuously, you cannot know what access brokers are finding. And if you don't know what they're finding, you cannot interrupt the chain before they monetize it.
Shrinking the Window: What Actually Works
The research on dwell time reduction is consistent: organizations that detect intrusions faster suffer dramatically lower financial impact. IBM's data shows that organizations with high levels of security AI and automation detected breaches 100 days faster than those without — and saved an average of $2.2 million in breach costs as a result. [2]
But detection is the reactive half of the equation. The proactive half is eliminating the exposures that give attackers their initial foothold in the first place — and doing so continuously, not annually.
Here is what the data says about where ransomware attackers actually gain initial access, according to the Sophos Active Adversary Report 2024: [1]
32% Exploited external vulnerabilities — top initial access vector Sophos Active Adversary Report, 2024 [1]
60% Of all breaches start externally IBM Cost of a Data Breach, 2023 [7]
29% Compromised credentials — often from exposed services Sophos Active Adversary Report, 2024 [1]
83% Of attacks leverage misconfigured or exposed assets Sprocket Security Intelligence [8]
What these numbers describe is an entirely preventable attack surface. External vulnerabilities and exposed credentials are not zero-day mysteries — they are findable, testable, and closeable. The problem is that most organizations only look for them once a year.
Continuous Testing as a Dwell Time Strategy
Reducing dwell time as a security outcome requires two things operating in parallel: better detection capability, and a continuously hardened external perimeter that removes the footholds attackers rely on for initial access. You cannot just detect faster if the door is still open.
Testing once a year means spending 364 days hoping nothing changed. That hope is not a security posture.
Continuous penetration testing addresses both halves. It provides the external adversarial perspective that confirms your perimeter's actual state — not its theoretical state from last year's report — while feeding a continuous remediation loop that closes exposures before attackers can stage them into dwell-time events.
The operational logic is straightforward. When your attack surface is continuously monitored and tested, new exposures are identified and validated within days of appearing — not months later at the next annual engagement. The window between "exposure created" and "exposure known" compresses dramatically. That compression directly reduces the attack surface available to ransomware operators and IABs.
Mandiant's M-Trends 2024 report notes that organizations with mature security testing programs — characterized by regular, adversarial validation of controls — consistently demonstrate faster detection times and lower-severity incident outcomes. [9] This is not correlation; it is causation. Organizations that know their exposure continuously are harder to dwell in.
What Security Leaders Should Demand From Their Programs
If you are responsible for security at an organization and ransomware is a board-level concern (and it should be), here are the questions your current program needs to answer:
- What is your current external attack surface, right now? Not as of your last pentest — today. Do you know every exposed domain, subdomain, open port, and vulnerable service? If the answer requires scheduling a conversation with a vendor, the answer is effectively "no."
- How quickly would you know if an attacker gained a foothold? This requires honest assessment of EDR coverage, log visibility, and behavioral monitoring — not just whether you have tools deployed, but whether those tools would surface attacker-like behavior before day 16.
- How long does it take you to close a critical external vulnerability after it's identified? If your mean time to remediate is 30+ days, then a newly disclosed CVE affecting your internet-facing infrastructure represents weeks of exploitable exposure.
- When were your backups last tested — and are they isolated from domain admin access? One of the most reliable ransomware preparation steps is compromising backup infrastructure first. Backups accessible by domain administrators are accessible by attackers who have achieved that privilege.
SPROCKET PERSPECTIVE
Exposure Windows Are Measurable. Dwell Time Is Reducible.
Sprocket's continuous penetration testing platform monitors your attack surface in real time and triggers expert-driven testing the moment new assets, vulnerabilities, or infrastructure changes appear. Every critical finding is validated by an OSCP or CISSP-certified human tester and alerted within 24 hours. The result is a continuously current picture of your actual exposure — the same picture ransomware operators are building about you, available to your team first.
The Bottom Line for Operations-Focused Security Leaders
Ransomware hitting your operations is not a question of if — statistically, it is a question of when and how bad. The "how bad" variable is almost entirely determined by dwell time, and dwell time is almost entirely determined by how quickly you can identify and close the exposures that enable initial access and lateral movement.
The data from Sophos, IBM, Mandiant, and Verizon all point to the same operational conclusion: organizations that operate with continuous visibility into their attack surface and test their defenses regularly suffer shorter dwell times, faster detection, and materially lower incident costs. Annual testing, by contrast, is a structural vulnerability — it creates predictable windows of blindness that sophisticated threat actors are explicitly trained to exploit.
The question is not whether you can afford continuous testing. The question — when you factor in the median cost of a ransomware incident, business interruption, regulatory exposure, and reputational damage — is whether you can afford what happens without it.
See Your Attack Surface Before Attackers Do
Sprocket's free Attack Surface Management scan gives you instant visibility into your exposed assets, open ports, DNS misconfigurations, and credential exposures — the same view an attacker or IAB would build before deciding you're worth targeting.
Get Your Free ASM Scan → sprocketsecurity.com
References
[1] Sophos. Active Adversary Report 2024. https://www.sophos.com/en-us/whitepaper/active-adversary-report
[2] IBM Security. Cost of a Data Breach Report 2024. https://www.ibm.com/reports/data-breach
[3] Ponemon Institute / IBM. Cost of a Data Breach Report 2023 — Impact of Dwell Time. https://www.ibm.com/reports/data-breach
[4] Coveware. Q4 2024 Ransomware Marketplace Report. https://www.coveware.com/ransomware-quarterly-reports
[5] Verizon. 2024 Data Breach Investigations Report (DBIR). https://www.verizon.com/business/resources/reports/dbir/
[6] Recorded Future. 2024 Annual Report: State of Ransomware. https://www.recordedfuture.com/research
[7] IBM Security. Cost of a Data Breach Report 2023. https://www.ibm.com/reports/data-breach
[8] Sprocket Security. Internal Intelligence — Attack Surface Exposure Statistics. https://www.sprocketsecurity.com
[9] Mandiant. M-Trends 2024: Special Report. https://www.mandiant.com/m-trends


