Security teams don’t wake up worrying about “future threats.” They worry about what they’re missing right now.
In 2026, the organizations that get breached won’t be the ones that ignored security. They’ll be the ones relying on offensive testing models that no longer match how their environments change.
Based on what we see every week in real customer environments, here are the top offensive security risks driving organizations to look beyond traditional pentesting, and how to address them.
“We Passed Our Pentest. Why Are We Still Exposed?”
What Organizations Are Worried About
“We just had a pentest. Why did this vulnerability show up?”
“Are we actually covered between tests?”
Why This Matters in 2026
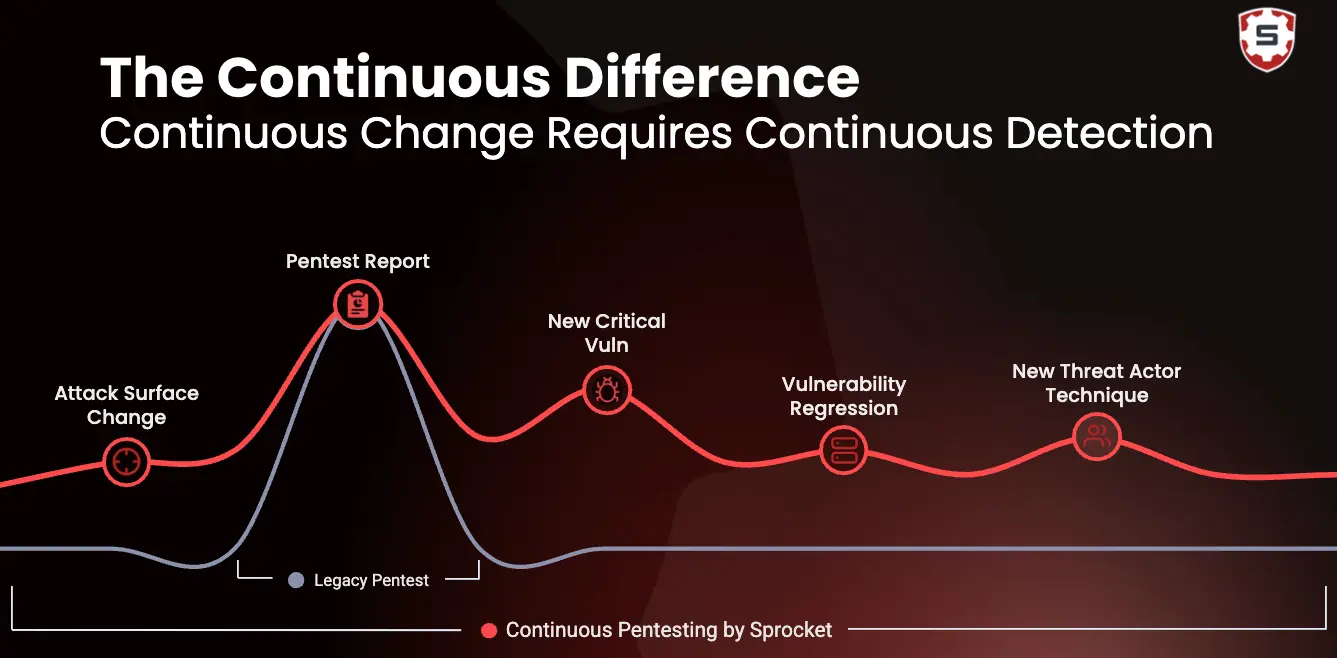
Point-in-time tests assume stability. Modern environments deploy continuously. The result is a growing window of untested change.
- New cloud resources spun up days after a pentest
- Feature flags exposing new logic paths
- Config changes that invalidate previous testing
What We See
“New assets, configuration drift, and untested features being pushing into production without testing. I've seen it all and when doing point-in-time testing the lag time between introduction and discovery of these issues can impact organizations from additional technical debt, data breach, and loss of trust which few can afford.” - Nick Berrie, Senior Penetration Tester
How Sprocket Security Helps
Even well-delivered PTaaS only validates a moment in time. Sprocket Security continuously tests as environments change, not after the fact. Exposures don’t silently accumulate between testing windows.
Identity Is the Real Attack Surface (And It’s Rarely Tested Well)
What Organizations Are Worried About
“Are our identity controls actually exploitable?”
“How do attackers bypass MFA and SSO?”
Why This Matters in 2026
Attackers increasingly don’t exploit servers. They exploit identities.
- MFA fatigue still works
- Over-privileged OAuth apps
- Broken authorization across SaaS and cloud platforms
What We See
“In most of our modern engagements, I’m not solely focused on exploiting vulnerable services running on servers anymore – that methodology works well for legacy style pentests. These days, identity misconfigurations are usually the path of least resistance. Over-scoped OAuth apps, lax SSO trust, or some “feature” that favors convenience over security are the focus areas. These don’t show up on a vulnerability scan and require a deeper, contextual understanding of the modern landscape.” - Nate Fair, Senior Penetration Tester
How Sprocket Security Helps
Identity failures are contextual. That’s why scanners and compliance checks miss them. They require human-led adversarial thinking, not checklists. Sprocket Security continuously test identity paths the way real attackers do; chaining misconfigurations across SSO, SaaS, and cloud identity layers.
“Low-Severity” Findings Are Leading to High-Impact Breaches
What Organizations Are Worried About
“Which findings actually matter?”
“What should we fix first?”
Why This Matters in 2026
Attackers don’t exploit vulnerabilities in isolation. They chain them together.
- Minor misconfigurations combined into full compromise
- Authorization flaws dismissed as “informational”
- Business logic abuse bypassing controls entirely
What We See
“Perform offensive security work long enough and you’ll know the sweet bliss that is brought by chaining multiple “low” & “informational” findings to full compromise. A verbose error message that leaks an internal API path, an IDOR leaking internal IDs, a JavaScript-driven path traversal (CSPT), and an overly permissive CORS policy – these are basically low severity and low impact. Chained together these issues build an exploitation & impact path that is greater than the sum of it’s parts.” - Nate Fair, Senior Penetration Tester
How Sprocket Security Helps
Traditional pentest reports fall short because severity scores don’t show attack paths. Sprocket Security focuses on exploitability and chaining, showing exactly how small issues become material risk.
Cloud & SaaS Sprawl Is Creating Blind Spots Attackers Love
What Organizations Are Worried About
“Do we even know what’s exposed?”
“How big is our external attack surface really?”
Why This Matters in 2026
Every SaaS app, API, integration, and cloud account expands the attack surface, often without security sign-off.
- Forgotten subdomains
- Orphaned APIs
- Over-permissioned SaaS integrations
What We See
“We often see organizations pushing out test environments that are forgotten about, acquiring companies that don't have as stringent security standards, or newly deployed applications and services that aren't quite ready for prime-time. With continuous testing it gives our team the flexibility to test these things as they're discovered, not when the next seasonal pentest comes around.” - Nick Berrie, Senior Penetration Tester
How Sprocket Security Helps
Asset inventories track what should exist, not what attackers can actually see. Sprocket Security continuously maps and tests real external exposure from an attacker’s point of view.
AI Isn’t Creating New Attacks. It’s Making Old Ones Faster
What Organizations Are Worried About
“Is AI changing how attackers operate?”
“Can we keep up?”
Why This Matters in 2026
AI doesn’t invent vulnerabilities. It compresses time-to-exploitation.
- Faster enumeration
- More effective phishing pretexts
- Rapid chaining of small flaws
What We See
“Last year, we saw several high-impact zero days across public-facing devices released in quick succession. A major concern going into this year is the race that begins the moment a patch or advisory is released. As AI continues to improve, it will increase the speed and ease of patch diffing and proof-of-concept development, lowering the bar for effective exploitation. This means the time between a disclosure, internet-wide scanning, and public exploit release will continue to shrink, leaving defenders with very little time to respond.” - Juan Pablo Gomez Postigo, Senior Penetration Tester
How Sprocket Security Helps
Point-in-time testing fails here because speed favors attackers when testing is episodic. Sprocket Security helps through continuous human-led testing that closes the speed gap. We validate exposures as fast as environments evolve.
Ransomware Isn’t the Problem. Initial Access Is
What Organizations Are Worried About
“How would ransomware get in?”
“Are we testing those paths?”
Why This Matters in 2026
Ransomware is the end of the story. Initial access is the part most organizations never test deeply enough.
- Stolen credentials
- Edge misconfigurations
- SaaS abuse leading to lateral movement
What We See
"Hacking isn't a magic button like how it is often portrayed in the movies. It's a methodical process even for the bad guys. Looking at the complete attack chain we understand how it's more efficient and effective to stop or delay progress at initial access instead of solely relying on sophisticated tools looking out for novel exploitation. In dynamic environments, it's critical to understand that new vectors for access are popping up all the time which is one strength of the continuous testing and validation we can provide at Sprocket." - Topher Lyons, Solutions Engineer
How Sprocket Security Helps
Most defenses fail because they focus on payloads, not entry points. Sprocket Security continuously validates how attackers gain access, before encryption, extortion, or impact.
Security Teams Are Being Asked to Prove Risk, Not Just Check Boxes
What Organizations Are Worried About
“How do we justify spend?”
“How do we show real risk reduction?”
Why This Matters in 2026
Boards and regulators increasingly want evidence of real-world exposure, not just completed audits.
- Security leaders being asked to explain actual business risk
- Why “passed” assessments don’t prevent incidents
- Number of tests or findings closed fail to reflect real-world exposure
What We See
“At Sprocket we find more and more clients are asking the right questions such as "what does this Finding or vulnerability mean for impact to my organization specifically". This shows a maturing understanding among clients that, while there may be a stream of vulnerabilities to constantly deal with, prioritization or remediation should be based on organization impact, not asset-specific impact.
Many of the traditional audit-driven "Check-Box" assessments tend to focus on specific line-item completions, regardless of their context to the organization. This can leave critical vulnerabilities that are not considered by check--box frameworks unattended, when a proper offensive security consultant is not involved to demonstrate the technical risk.” - Nick Aures, Senior Penetration Tester
How Sprocket Security Helps
Point-in-time testing cannot answer what’s changed since an organization’s last test, what’s exploitable today, or whether fixes actually closed attack paths. Sprocket Security’s continuous testing provides ongoing proof of exposure reduction, not stale reports.
Conclusion: 2026 Rewards Continuous Offense, Not Periodic Validation
The biggest mistake organizations will make in 2026 is assuming that better pentesting delivery solves a timing problem. Teams that stay ahead will test as often as they deploy, prioritize exploitability over severity, and treat offensive security as continuous instead of annual.
Sprocket Security exists to answer one question: What can an attacker exploit in our environment right now? Reach out to our team today to find out how we can answer that question for you in 2026!