Introduction
When starting a penetration test, we first try to discover domains associated with our target apex domain. To help you navigate this part of the process, we’re going to detail it, highlighting tips and tricks for working around registrant privacy services and other roadblocks you may face.
DNS Essentials and Vocab
If you are unfamiliar with domain nomenclature, I have included a list of vocabulary words and additional learning resources below to hopefully catch everyone up to speed.
Apex Domain
An apex domain is a root domain that doesn’t contain a subdomain.
Examples: example.com is an apex domain because it doesn’t have a subdomain. www.example.com is not an apex domain because it contains the subdomain part www.
Subdomain
A subdomain is the part of a URL before the root domain. You can configure your subdomain as www or as a distinct section of your site, like blog.example.com.
Whois Records
A Whois record contains all of the contact information associated with the person, group or company that registers a particular domain name.
Top-Level Domain (TLD)
The term top-level domain, or TLD, refers to the first part of every domain name. For example, in the domain name example.com, the TLD is COM.
Learning Resources
If you’re totally lost, I recommend walking through the guided learning resource, How DNS works, for a clear explanation of DNS.
Whoxy for searching
Often, we start with only a single apex domain for initial reconnaissance. We, however, want to take that domain and uncover any associated records to get more coverage during our engagement. The best source for this, in my experience, is the site linked below.
There is also a great command-line tool that uses Whoxy for searches. It is linked below and requires an API key to function properly.
Easy Apex Domain Discovery
With Whoxy, you can quickly search for records associated with your target domain. For example, let’s target the domain upwork.com. Searching this domain on Whoxy presents the results shown below.

The items under each header are relevant to us. Clicking on the registrant contact’s name, for example, reveals several domains.

During our reconnaissance phase, these will come in handy. I recommend taking note of them for future analysis. In addition to domains associated with the registrant’s name, nearly a thousand domains are associated with the Upwork company registrar.

Whoxy won’t even show us all of these using the web interface. Use the command-line tool I linked earlier to easily download all of these domains. Use the directions included in the GitHub repository to install it, and export your Whoxy API key in your terminal session.

A snippet of output is shown above.
Historical Records
Something you’re going to see a lot as a tester are search results similar to what’s shown below.

In this example, all we see is fairly anonymized records for the domain, plex.tv. Don’t fret. Whoxy stores historical DNS and Whois records for domains. Scrolling down to the bottom of the page reveals what we’re looking for.

It only takes an organization slipping up once for us to quickly find the information we want. Several times I’ve seen an organization use a domain purchase anonymizer service for years, only to have registered things personally, just once, five years ago. With plex.tv we can now look through associated records to widen our overall scope.
Reaching for the stars
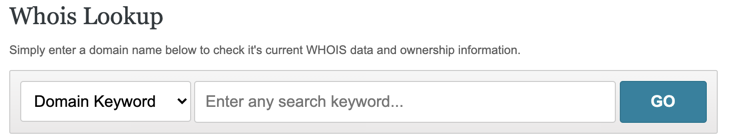
Let’s say an organization has used a registration anonymization service for years and never slipped up. What then? It’s very likely that they have still, at one point, Try Whoxy’s domain keyword feature. This is hit or miss and requires a lot of manual review. When doing this, switch your search method to “Domain Keyword” and start digging through the results.
Review your results
We need to make sure we aren’t including a superfluous number of domains in our scope, as it can often take up much more time during testing than it’s worth.
Let’s take Upwork for example. When reviewing our results, we need to ask ourselves: Did Upwork buy these domains for other aspects of business operations or only to squash any type of domain squatting? You can tell if that’s the case if: Most domains are similar, but with different TLDs * If you navigate to the apex domains in a browser, and you’re subsequently redirected to the primary company website
I will often see inexperienced testers attempting to leverage domains that are irrelevant in the grand scheme of their engagement. Use your clients allocated testing time wisely to always provide the most value.
Wrap Up
Discovering domains associated with your target can make the difference during an engagement. Make sure you take the time to review results from Whoxy and related tooling to get the best coverage possible.
This form of reconnaissance is an essential step for building a quality continuous penetration testing platform. Be thorough and it will make the remaining testing process more effective and efficient.