The fear is familiar to every security leader: an auditor is coming in six weeks, and you haven't touched your penetration test report since it landed nine months ago. In that time, three engineers joined, two cloud instances spun up, a new SaaS tool got provisioned without your knowledge, and two CVEs dropped against your web framework. But your report still says you're clean.
This is the gap that keeps CISOs up at night, and it's precisely the gap that continuous penetration testing is designed to close. Not just for security's sake, but because the compliance and audit landscape has fundamentally changed, and point-in-time testing can no longer keep pace with it.
The Problem With Annual Testing (And Audit Season)
Annual penetration testing was designed for a slower era: when infrastructure changed quarterly at most and compliance frameworks validated a static snapshot of security controls. Today, organizations deploy code daily, spin up cloud resources on demand, and acquire SaaS tools without formal procurement. Your attack surface is in constant motion.
Frameworks like SOC 2, PCI DSS v4, ISO 27001, HIPAA, and CMMC all require evidence of penetration testing, but the auditor sitting across the table knows what security leaders often won't say out loud: a report from eight months ago doesn't tell you much about where you stand today.[1]
"A traditional external pen test is a single snapshot in time. Sprocket Security offers that testing on a continuous basis, so we always have an up-to-date view." — IT Lead, Services Industry (Gartner Peer Insights)
According to Gartner, Penetration Testing as a Service (PTaaS) is now a recognized category, driven largely by the industry's shift away from point-in-time engagements toward continuous validation.[2] The reason is straightforward: a breach doesn't wait for your next scheduled test. Neither should your assurance program.
What Frameworks Actually Require (And What They Imply)
Compliance requirements around penetration testing are tightening across every major framework. Understanding what auditors are looking for and what best practice looks like beyond the minimum is the first step toward building a posture that's permanently audit-ready.
PCI DSS v4 Requirement 11.4 Annual pen testing required; additional testing after significant infrastructure or application changes. v4 emphasizes continuous risk assessment over annual cycles.[3]
SOC 2 CC7.1 / CC4.1 Monitoring of system components and risk assessment required on an ongoing basis. Auditors increasingly expect evidence of continuous testing activity.[4]
ISO 27001:2022 Annex A 8.8 Management of technical vulnerabilities, including regular pentesting, must be demonstrably systematic, not episodic.[5]
CMMC 2.0 CA.L2-3.12.1 Periodic assessment of security controls required for defense contractors. Level 2 and above require third-party assessments validating ongoing posture.[6]
THE AUDITOR'S UNSTATED QUESTION
When a SOC 2 or PCI auditor reviews your penetration test report, they're not just checking the box - they're asking: "Is this organization actually secure today, or just on the day of the test?" Continuous testing gives you a defensible answer.
How Continuous Penetration Testing Closes the Gap
Continuous penetration testing doesn't replace the rigorous assessment you need for compliance it extends and amplifies it. Rather than testing once and hoping nothing changes, a continuous model means that every significant change to your environment triggers expert-driven validation. Here's how that flow works in practice:
PHASE 1 Initial Penetration Test & Baseline
A thorough expert-led test establishes your baseline. Every finding is documented with proof-of-concept evidence, CVSS scoring, and clear remediation guidance directly usable as audit evidence.
PHASE 2 Attack Surface Monitoring (Continuous)
Automated monitoring watches for new subdomains, exposed services, cloud drift, credential exposure, and infrastructure changes 24/7, not just on testing days.
PHASE 3 Change-Triggered Expert Testing
When your environment changes, a new asset appears, a new CVE drops against your stack, or a misconfiguration is detected, human testers are automatically engaged to validate the risk.
PHASE 4 On-Demand Compliance Reporting
At any point in the year, you can generate a current, evidence-backed compliance report from live data, not a snapshot from last spring.
According to a 2024 Ponemon Institute study, organizations with a mature security testing program including continuous validation reduced their mean time to identify a breach by an average of 74 days compared to organizations relying on periodic assessments alone.[7] Faster identification means smaller blast radius, lower remediation cost, and a far cleaner story to tell auditors.
Continuous vs. Annual: The Audit-Readiness Comparison
The gap between a point-in-time penetration test and a continuous model isn't just philosophical it shows up directly in what you can demonstrate to auditors, regulators, and your board.
Audit Requirement | Sprocket Continuous Testing | Annual / Point-in-Time |
|---|---|---|
Evidence of testing coverage | ✓ Live portal with full activity log and findings history | ✗ Static PDF, often months old |
Testing after significant changes | ✓ Automated change detection triggers new testing | ✗ Requires manually scheduling a new engagement |
Vulnerability remediation proof | ✓ Unlimited retesting verifies every fix | ✗ Retest typically costs extra; often skipped |
On-demand compliance report | ✓ Generated from live data at any time | ✗ Fixed to the date of the original engagement |
Attack surface visibility | ✓ Continuous ASM monitors all assets in real time | ✗ Scoped to assets known at time of test only |
Human-validated findings | ✓ 100% of findings validated by expert testers | ✗ Varies widely; scanner output common |
The Real Risk Security Leaders Are Carrying
The scenario security leaders fear most isn't failing an audit: it's experiencing a breach in the window between audits. According to Verizon's 2024 Data Breach Investigations Report, 68% of breaches involved a non-malicious human element, and most successful attacks exploited known vulnerabilities that had been present for months before discovery.[8]
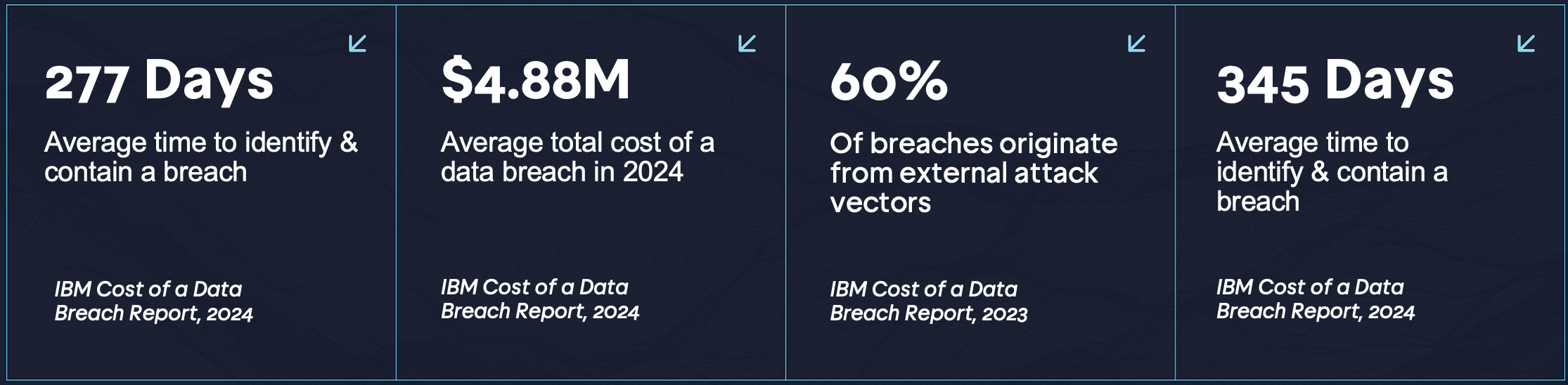
This means the 345 days between annual tests aren't just a compliance gap - they're an operational liability. Every unmonitored new asset is a potential entry point. Every unpatched service that appears post-assessment is exposure that your annual report will never capture.
A breach that occurs after a clean audit report doesn't just cost money - it destroys the credibility of your entire security program. The average cost of a data breach in 2024 reached $4.88 million, a 10% increase over 2023, with breaches involving critical infrastructure costing significantly more.[9] That cost doesn't include regulatory fines, reputational damage, or the erosion of customer trust that follows public disclosure.
Building an Audit-Ready Posture Year-Round
For security leaders in financial services, SaaS, technology, and retail, industries under the heaviest compliance pressure, the shift to continuous testing isn't a nice-to-have. It's becoming the expectation. Here's what a permanently audit-ready posture looks like in practice:
1. Start with attack surface visibility
You can't test what you don't know exists. Free Attack Surface Management (ASM) gives you a continuously updated, attacker-eye view of your exposed assets, domains, subdomains, cloud services, APIs, and credentials, before testing begins. This is the foundation that makes continuous testing possible.
2. Establish a tested baseline
An initial penetration test establishes what your environment looks like today and creates the documented evidence auditors expect. Every finding arrives with proof-of-concept exploit, CVSS score, affected hosts, and clear remediation steps formatted for audit use from day one.
3. Let change drive testing
Rather than scheduling tests manually, mature programs use change detection to automatically scope and trigger expert testing when new assets appear, infrastructure shifts, or known CVEs emerge against your stack. Your test coverage grows with your environment - not months behind it.
4. Retest until it's fixed - no extra invoices
Unlimited retesting is the operational unlock that makes remediation real. When your team patches a finding, they need to confirm it's actually resolved - not schedule another engagement and wait weeks. Continuous programs include retesting as a core capability, not an add-on.
5. Generate compliance evidence on demand
When your auditor asks for penetration test evidence, you generate a current report from live, continuously updated data, not a PDF with a date from last spring. SOC 2, ISO 27001, HIPAA, PCI, and CMMC reports are available on demand, mapping findings directly to framework requirements.
THE SPROCKET DIFFERENCE
Sprocket's platform delivers findings in real time via the Sprocket Portal with role-based reporting for both security teams and leadership enabling faster, aligned remediation without waiting weeks for a static PDF. OSCP & CISSP-certified testers validate 100% of findings. Every critical finding triggers an alert in under 24 hours.
The Bottom Line for Security Leadership
Audit readiness used to mean having a clean pen test report in a drawer. Today it means being able to demonstrate, at any moment, that you understand your current attack surface, that you've tested against it recently, and that you're closing findings faster than attackers can exploit them.
That's not what annual testing delivers. It's exactly what continuous penetration testing is built for.
For security leaders in mid-market organizations, typically 250 to 2,000 employees, continuous testing is also the practical answer to limited internal resources. Your platform handles the monitoring. Expert testers handle the validation. Your team focuses on remediation with confidence that the work is verified.
The next audit shouldn't be a fire drill. With continuous penetration testing, it's just another day where your documentation is already current.
See Your Attack Surface Before Your Auditor Does
Start with free Attack Surface Monitoring. Discover your exposed assets in minutes.
https://www.sprocketsecurity.com/solutions/attack-surface-management
References
- IBM Security. Cost of a Data Breach Report 2024. IBM Corporation, 2024. ibm.com/reports/data-breach
- Market Guide for Penetration Testing as a Service (PTaaS). Gartner Research, 2024.
- PCI Security Standards Council. PCI DSS v4.0 Requirements and Testing Procedures. Requirement 11.4, March 2022. pcisecuritystandards.org
- Trust Services Criteria (TSC) for SOC 2. CC7.1 — System Monitoring; CC4.1 — Risk Assessment, 2022.
- ISO/IEC 27001:2022 — Information Security Management Systems. Annex A, Control 8.8: Management of Technical Vulnerabilities.
- Office of the Under Secretary of Defense. CMMC Model v2.0 Documentation. U.S. Department of Defense, 2021.
- Ponemon Institute. The State of Vulnerability Management in DevSecOps. Sponsored by Rezilion, 2024.
- 2024 Data Breach Investigations Report (DBIR). Verizon Business, 2024. verizon.com/business/resources/reports/dbir/
- IBM Security. Cost of a Data Breach Report 2024. Average total cost figure: $4.88M USD globally.


